Notespaceos
spaceos 时间:2021-03-28 阅读:()
One-byteModificationforBreakingMemoryForensicAnalysisTakahiroHaruyama/HiroshiSuzukiInternetInitiativeJapanInc.
forsubmissionMemoryForensicsOverview–MemoryAcquisition–MemoryAnalysisPreviousWorks:AntiMemoryForensicsProposedAntiAnalysisMethodImprovementPlansWrap-upSummary2MEMORYFORENSICSOVERVIEW3Analyzingvolatiledataisimportanttodetectthreatsquickly–increasingamountsofdiskdata–antidiskforensicmethodsusedbymalwaresMemoryforensicsbecamepopularoverthelastfewyears2stepsformemoryforensics–memoryacquisitionandmemoryanalysis4What'sMemoryForensicsTargetMachineInvestigator'sMachineMemoryImageFile1.
AcquireRAMdataasanimagefile2.
ParseandanalyzetheimageofflineOfflineparsingamemoryimagedoesn'tusesystemAPIsMemoryforensicscanget–unallocateddata(e.
g.
,terminatedprocess)–datahiddenbymalware(e.
g.
,hiddenprocess)5WhyMemoryForensicsLiveResponseToolMemoryForensicAnalysisToolRunningProcessHiddenProcessTerminatedProcessAllocatedUnallocatedWindowsAPIParsebinaryimageandextractinformationfromitGetinformationthroughsystemAPIRawImageAcquisition–HBGaryFastDumpPro[1]–GuidanceWinEn[2]–MoonSolsWindd[3]CrashDumpImageAcquisition–MoonSolsWinddMemoryImageConversion–MoonSolsWindowsMemoryToolkit[3]6SomeFormats/AcquisitonToolsMemoryImageFileCPURegisterIncludedCrashDumpHibernationNotIncludedRawDifferencebetweenRawImageandCrashDumpCrashdumpfiledoesn'tinclude–1stPage–PagesreservedbydevicesRun[0]BasePage=0x1,PageCount=0x9eRun[1]BasePage=0x100,PageCount=0xeffRun[2]BasePage=0x1000,PageCount=0xeef0Run[3]BasePage=0xff00,PageCount=0x1001stPage(BIOSReserved)AddressSpaceReservedbyDevices(NotIncludedincrashdump)PhysicalMemoryAddressSpace(e.
g.
,256MBRAM)7EvaluationofMemoryAcquisitionToolsCanrawimageacquisitiontoolsget1stpageanddevice-reservedpages[4]–WinEn–Win32dd/c0MemoryContent(/c)option–Caution:/c0optionmaycauseBSODonx64machineWinEnFDProWin32dd/c0Win32dd/c1Win32dd/c21stPageDevicereservedpages8AnalysisExample:MakingObjectCreationTimeline9VolatilityFramework[5]–timelinerplugin[6]usedkernelobjects(process/thread/socket)eventlogsSpyEyebot(deadprocess)TCPconnectionestablishedbyexplorer.
exeCodeinjectionactivityAnalysisExample:DetectingCodeInjection10Detectingcodeinjection–VolatilityFrameworkmalfind–EnCaseEnScript[7]VadDump–MandiantRedline[8](GUIfront-endforMemoryze[9])ThetoolscheckprotectionflagofVirtualAddressDescriptorMandiantRedline(Memoryze)HBGaryResponderVolatilityFramework2.
0EnCaseEnScirptSupportedWindowsOSAllAllXP/Vista/7/2003/2008XP/7/2003/2008SupportedImageFormatRawRawRawCrashdumpHibernationRawCrashdumpSupportedCPUArchitectureIntelx86AMDx64Intelx86AMDx64Intelx86Intelx86AMDx64Extractingdeadprocess/closedconnectionNoNoYesYesNoteMalwareRiskIndex,MemD5DigitalDNA,codegraphingOpensource,richpluginsMultilingualsearch,EntropyComparisonofMemoryAnalysisTools11PREVIOUSWORKS:ANTIMEMORYFORENSICS12ShadowWalkerisproposedbySherriSparksandJamieButlertohidemaliciousmemoryregions–Installedpagefaulthandlermakesde-synchronizedDTLB/ITLBdataaccess->randomgarbagedataexecuteaccess->rootkitcodeMemoryacquisitiontoolscannotpreventShadowWalkerfromhidingmemorypages–ButAnalysistoolscandetecttheIDThooking13AntiAcquisitionMethods:ShadowWalker[10]Proofofconceptscript–killingspecifiedprocessesorpreventingdriverloadingswiththeaimofmemoryacquisitionfailureVeryeasytoimplement–Theevasionisalsoeasy(e.
g.
,randomname)–Preventingdriverloadingshasanimpactontherunningsystem14AntiAcquisitionMethods:MeterpreterAntiMemoryForensicsScript[11]Objectcarvingisonetechniquetoextractkernelobjectinformation–e.
g.
,processobject(_EPROCESS)PTFinder:Type/Sizein_DISPATCHER_HEADERVolatilityFramework:PoolTagin_POOL_HEADERBrendanDolan-Gavittetal.
warnedanattackercouldchangethevaluestohideaspecifiedobject[12]–Instead,theyproposedrobustsignaturescausingBSODorfunctionalityfailuresifthevaluesarechanged15AntiAnalysisMethod:AntiObjectCarvingmodifyingheadervaluesofcmd.
exeClosed-sourceanalysistoolscanfindthehiddenprocess–HowdotheyfinditOtherthanobjectcarving,thereareseveralkeyoperationsforanalyzingmemoryimage–TheoperationsarerobustLet'scheckit!
16AntiAnalysisMethod:AntiObjectCarving(Cont.
)MemoryzeHBGaryResponderPROPOSEDANTIANALYSISMETHOD17Researchedimplementationsofthreemajortools–VolatilityFramework2.
0–MandiantMemoryze2.
0–HBGaryResponderCommunityEdition2.
0Foundthreeoperationsexecutedinmemoryanalysisincludeafewunconsideredassumptions–Proposedmethodmodifiesone-byteofdatarelatedtotheoperationsThedataisdefinedas"AbortFactor"–Itcan'thidespecificobjects,butcanabortanalyses–NoimpactontherunningsystemNoBSOD,noerrorsforafewdaysto2weeks18AbstractofProposedMethodVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingkernelobjects–traversinglinkedlistsorbinarytrees–objectcarving19SensitiveThreeOperationsinMemoryAnalysisVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingkernelobjects–traversinglinkedlistsorbinarytrees–objectcarving20SensitiveThreeOperationsinMemoryAnalysisOSswitchesitscontextbyloadingDirectoryTableBase(DTB)ofeachprocess–DTBisstoredineachprocessobject(_EPROCESS)Initially,analysistoolsmustgetDTBvalueforkernelspaceTwoprocesseshavethekernelDTB–PsInitialSystemProcess(Systemprocess)–PsIdleProcess(Idleprocess)21VirtualAddressTranslationinKernelSpaceOSloadsDirectoryTableBase(Startphysicaladdressforaddresstranslation)intoControlRegister(CR3)x86AddressTranslation-HowPAEX86Workshttp://technet.
microsoft.
com/en-us/library/cc736309(WS.
10).
aspx22VirtualAddressTranslationinKernelSpace:ProcessObjectStructure_POOL_HEADER_OBJECT_HEADER_EPROCESS_KPROCESS_DISPATCHER_HEADERPoolTag:"Pro"TypeandSizeDTBImageFileName:"System"or"Idle"FlagsSearch_DISPATCHER_HEADERtoget_EPROCESSCheckwhethertheImageFileNameis"Idle"–IftheprocessisIdle,getDTBvaluein_KPROCESS23VirtualAddressTranslationinKernelSpace:VolatilityFramework_DISPATCHER_HEADER(e.
g.
,"x03x00x1bx00")ImageFileNameSearch"System"tofindImageFileNamein_EPROCESSofPsInitialSystemProcessValidatebyusing_DISPATCHER_HEADERinthe_KPROCESS–All_DISPATCHER_HEADERpatternsarechecked24VirtualAddressTranslationinKernelSpace:MandiantMemoryzeOSversion_DISPATCHER_HEADERByteSequenceXP32bit03001B00200332bit03001E00200364bit03002E00Vista32bit03002000Vista64bit03003000732bit03002600764bit03005800Validatebyusingthefollowingvalues–Flagsin_OBJECT_HEADERThedistancebetweenPoolTagand_EPROCESSiscalculatedaccordingtothevalue–PoolTagin_POOL_HEADERSearchPoolTagfrom_EPROCESSpositionandcheckwhetherthesearchhitoffsetisequaltothecalculateddistanceIfalldataisvalid,gettheDTBvalue25VirtualAddressTranslationinKernelSpace:MandiantMemoryze(Cont.
)Search_DISPATCHER_HEADERstoget_EPROCESSGetDTBvaluefromtheresultandvalidateitResponderseemstobeequippedwiththealgorithmguessingkernelDTB–IfDTBsofPsInitialSystemProcessandPsIdleProcessarenotfound,aguessedDTBvalueisused26VirtualAddressTranslationinKernelSpace:HBGaryResponder27VirtualAddressTranslationinKernelSpace:RelatedDataToolRelatedDataAbortFactorRemarksVolatilityFramework_DISPATCHER_HEADERXPsIdleProcessImageFileNamein_EPROCESSXMandiantMemoryze_DISPATCHER_HEADERXPsInitialSystemProcessPoolTagin_POOL_HEADERXFlagsin_OBJECT_HEADERXImageFileNamein_EPROCESSXHBGaryResponder_DISPATCHER_HEADERoriginalguessingalgorithmVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingKernelObjects–traversinglinkedlistsorbinarytrees–objectcarving28SensitiveThreeOperationsinMemoryAnalysisSizeanddefinitionofkerneldatastructuresdifferaccordingto–OSversion(e.
g.
,XPSP2/SP3,7SP0/SP1)–architecture(x86andx64)Allanalysistoolsguesstheversionusingdebugstructures29GuessingOSversionandArchitectureOSversion_EPROCESSsize(bytes)WindowsXPSP332bit0x260Windows7SP032bit0x2C0Windows7SP064bit0x4D0WindowsVistaSP232bit0x270WindowsVistaSP264bit0x3E830GuessingOSversionandArchitecture:DebugStructuresandKeyValues_KPCR_DBGKD_GET_VERSION64_KDDEBUGGER_DATA64KdVersionBlockDebuggerDataListHeaderCmNtCSDVersion_DBGKD_DEBUG_DATA_HEADER64OwnerTag:"KDBG"SizeKernBaseKernBasePrcbDataPsActiveProcessHeadPsLoadedModuleList_KPRCBCurrentThreadUsersmustspecifyOSversionandArchitecture–e.
g.
,--profile=WinXPSP2x86Iftheversionisunknown,imageinfocommandcanguessit–scan_DBGKD_DEBUG_DATA_HEADER64[13]31GuessingOSversionandArchitecture:VolatilityFrameworkOwnerTag:"KDBG"SizeSupposedlydetermineOSandarchitecturebasedon_DISPATCHER_HEADERValidatethembyusinganoffsetvalueofImageFileNamein_EPROCESS32GuessingOSversionandArchitecture:MandiantMemoryzeOSversionoffsetvalueofImageFileNameXP32bit0x174200332bitSP00x154200332bitSP1/SP20x164XP/200364bit0x268Vista32bit0x14CVista64bit0x238732bit0x16C7/200864bit0x2E0TrytotranslateavirtualaddressofThreadListHeadin_KPROCESS–Ifpossible,theOSversionandarchitecturearecorrectGetSPversionfromCmNtCSDVersionin_KDDEBUGGER_DATA6433GuessingOSversionandArchitecture:MandiantMemoryze(Cont.
)GetKernBasevalue–_DBGKD_GET_VERSION64or_KDDEBUGGER_DATA64ValidatethePEheadersignatures–DOSheader"MZ"andNTheader"PE"GetOSversion–OperatingSystemVersionsinOptionalHeadere.
g.
,Windows7–MajorOperatingSystemVersion=6–MinorOperatingSystemVersion=1Getmorespecificversion–TimeDataStampinFileheader34GuessingOSversionandArchitecture:HBGaryResponder35GuessingOSversionandArchitecture:RelatedDataToolRelatedDataAbortFactorRemarksVolatilityFramework_DBGKD_DEBUG_DATA_HEADER64XMandiantMemoryze_DISPATCHER_HEADERXPsInitialSystemProcessoffsetvalueofImageFileNameXThreadListHeadin_KPROCESSCmNtCSDVersionin_KDDEBUGGER_DATA64HBGaryResponderKernBasein_DBGKD_GET_VERSION64or_KDDEBUGGER_DATA64PEHeaderofWindowskernelPEheadersignatures"MZ"/"PE"OperatingSystemVersioninOptionalHeaderXTimeDataStampinFileHeaderVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingKernelObjects–traversinglinkedlistsorbinarytrees–objectcarving36SensitiveThreeOperationsinMemoryAnalysisTraversinglinkedlistsorbinarytrees–Generally,usespeciallead/rootaddressesPsActiveProcessHeadforprocesslistPsLoadedModuleListforkernelmodulelistVadRootforVirtualAddressDescriptortreeObjectcarving–Generally,usefixedvaluesinheaders_POOL_HEADER_DISPATCHER_HEADERMyresearchfocusedongetting_EPROCESS37GettingKernelObjectsProcesslististwo-waylink–Each_EPROCESSincludesActiveProcessLinks_LIST_ENTRY(FlinkandBlink)–PsActiveProcessHeadandPsInitialSystemProcessarebounduptogether38GettingKernelObjects:ProcessLinkedListPsActiveProcessHead_EPROCESS"System"_EPROCESS"smss.
exe"_EPROCESS"win32dd.
exe"FLINKBLINKFLINKBLINKFLINKBLINKFLINKBLINK.
.
.
.
.
.
.
.
.
Traversinglinkedlistsorbinarytrees–Search_DBGKD_DEBUG_DATA_HEADER64–getPsActiveProcessHeadin_KDDEBUGGER_DATA64Objectcarving–usePoolTagin_POOL_HEADER39GettingKernelObjects:VolatilityFrameworkExecutingKDBGScannerGetting_DBGKD_DEBUG_DATA_HEADER64(=_KDDEBUGGER_DATA64)addressObjectcarving–find_EPROCESSusingaddressvaluese.
g.
,–DTBis0x20-bytesaligned–(Peb&0x7ffd0000)==0x7ffd0000–(ActiveProcessLinks.
Flink&0x80000000)==0x80000000–similartorobustsignaturesproposedbyBrendanDolan-Gavittetal.
[12]40GettingKernelObjects:MandiantMemoryzeTraversinglinkedlistsorbinarytrees–getCurrentThreadin_KPRCB–get_EPROCESSfromthethreade.
g.
,ApcState.
Processin_KTHREAD(XP)–starttotraverseprocesslistfromthe_EPROCESS"System"stringiscomparedwithImageFileNameof_EPROCESS–foridentifyingPsActiveProcessHead–fordetectinghiddenprocess41GettingKernelObjects:HBGaryResponder42GettingKernelObjects:RelatedDataToolRelatedDataAbortFactorRemarksVolatilityFramework_DBGKD_DEBUG_DATA_HEADER64XPsActiveProcessHeadin_KDDEBUGGER_DATA64XPoolTagin_POOL_HEADERMandiantMemoryzeaddressvaluesin_EPROCESS(DTB,Peb,etc.
)HBGaryResponderCurrentThreadin_KPRCBPsInitialSystemProcess_EPROCESSpointerin_KTHREADImageFileNamein_EPROCESSX43AbortFactorsToolVirtualAddressTranslationinKernelSpaceGuessingOSversionandArchitectureGettingKernelObjectsVolatilityFramework2factors:_DISPATCHER_HEADERandImageFileName(PsIdleProcess)1factor:_DBGKD_DEBUG_DATA_HEADER642factors:_DBGKD_DEBUG_DATA_HEADER64andPsActiveProcessHeadMandiantMemoryze4factors:_DISPATCHER_HEADER,PoolTag,FlagsandImageFileName(PsInitialSystemProcess)2factors:_DISPATCHER_HEADERandoffsetvalueofImageFileName(PsInitialSystemProcess)NoneHBGaryResponderNone1factor:OperatingSystemVersionofkernelheader1factor:ImageFileName(PsInitialSystemProcess)Loadakerneldriverintox86XPVM–Thedrivermodifies1byteofthefollowingdataSizein_DISPATCHER_HEADERofPsIdleProcessPoolTagin_POOL_HEADERofPsInitialSystemProcessMajorOperatingSystemVersioninPEheaderofWindowskernelCheckthemodificationusingWinDbgAcquirethememoryimageusingLiveCloudKd[14]Analysisusingthreetools44DemousingPoCDriver(Video)IMPROVEMENTPLANS45GuessingbasedonaddressvaluesMinimumguessingSeparatingimplementationstogetkernelobjects46ImprovementPlansThemodificationofaddressvaluesoftencausesBSODorfunctionfailures–_EPROCESSobjectcarvingbyMemoryze–_KPCRobjectcarvingbyVolatilityFramework[15]47GuessingBasedonAddressValues_KPCRaddress==SelfPcrand_KPRCBaddress==PrcbSupportcrashdumpformat–Registervaluescannotbemodified48Minimumguessing(1)DataincrashdumpheaderExtractedfrom(Win32ddimplementation)AbortFactorDTBCR3registerOSversionnt!
NtBuildNumberXPAEenabledCR4registerPsActiveProcessHead_KDDEBUGGER_DATA64XPsLoadedModuleList_KDDEBUGGER_DATA64XSupportargumentpassingoptionsaboutDTBandOSversion–VolatilityFrameworksupportsthemspecifyOSversionbyusing"--profile"optionspecifyDTBvaluebyusing"--dtb"option49Minimumguessing(2)IfDTBvaluecannotbeacquired,displaytheresultminimally-extractedbyobjectcarving50SeparatingimplementationstogetkernelobjectsGettingtheseinformationdoesn'tneedDTBvalueWRAP-UP51Proposedantianalysismethodcanabortmemoryanalysistoolsbymodifyingonlyone-byte–ThemethodiseffectiveformemoryimagesofallOSversionsandarchitectures–Abouttheimpactontherunningsystem,longtermevaluationsmaybeneededIhope–Developersimprovetheimplementations–Usersfigureoutinternalsofmemoryanalysisanddealwithanalysiserrors52Wrap-up53Questions(twitter:@cci_forensics)PleasecompletetheSpeakerFeedbackSurveys!
[1]HBGaryFastDumpPro[2]EnCaseWinEn(build-intoolofEnCase)[3]MoonSolsWindowsMemoryToolkit[4]ReservedAddressSpaceinWindowsPhysicalMemory[5]VolatilityFramework[6]timelinerplugin[7]Update:MemoryForensicEnScript[8]MandiantRedline[9]MandiantMemoryze[10]"SHADOWWALKER"RaisingTheBarForRootkit[11]MeterpreterAntiMemoryForensics(Memoryze)Script[12]RobustSignaturesforKernelDataStructures[13]IdentifyingMemoryImages[14]YOURCLOUDISINMYPOCKET[15]FindingObjectRootsinVista(KPCR)54References
forsubmissionMemoryForensicsOverview–MemoryAcquisition–MemoryAnalysisPreviousWorks:AntiMemoryForensicsProposedAntiAnalysisMethodImprovementPlansWrap-upSummary2MEMORYFORENSICSOVERVIEW3Analyzingvolatiledataisimportanttodetectthreatsquickly–increasingamountsofdiskdata–antidiskforensicmethodsusedbymalwaresMemoryforensicsbecamepopularoverthelastfewyears2stepsformemoryforensics–memoryacquisitionandmemoryanalysis4What'sMemoryForensicsTargetMachineInvestigator'sMachineMemoryImageFile1.
AcquireRAMdataasanimagefile2.
ParseandanalyzetheimageofflineOfflineparsingamemoryimagedoesn'tusesystemAPIsMemoryforensicscanget–unallocateddata(e.
g.
,terminatedprocess)–datahiddenbymalware(e.
g.
,hiddenprocess)5WhyMemoryForensicsLiveResponseToolMemoryForensicAnalysisToolRunningProcessHiddenProcessTerminatedProcessAllocatedUnallocatedWindowsAPIParsebinaryimageandextractinformationfromitGetinformationthroughsystemAPIRawImageAcquisition–HBGaryFastDumpPro[1]–GuidanceWinEn[2]–MoonSolsWindd[3]CrashDumpImageAcquisition–MoonSolsWinddMemoryImageConversion–MoonSolsWindowsMemoryToolkit[3]6SomeFormats/AcquisitonToolsMemoryImageFileCPURegisterIncludedCrashDumpHibernationNotIncludedRawDifferencebetweenRawImageandCrashDumpCrashdumpfiledoesn'tinclude–1stPage–PagesreservedbydevicesRun[0]BasePage=0x1,PageCount=0x9eRun[1]BasePage=0x100,PageCount=0xeffRun[2]BasePage=0x1000,PageCount=0xeef0Run[3]BasePage=0xff00,PageCount=0x1001stPage(BIOSReserved)AddressSpaceReservedbyDevices(NotIncludedincrashdump)PhysicalMemoryAddressSpace(e.
g.
,256MBRAM)7EvaluationofMemoryAcquisitionToolsCanrawimageacquisitiontoolsget1stpageanddevice-reservedpages[4]–WinEn–Win32dd/c0MemoryContent(/c)option–Caution:/c0optionmaycauseBSODonx64machineWinEnFDProWin32dd/c0Win32dd/c1Win32dd/c21stPageDevicereservedpages8AnalysisExample:MakingObjectCreationTimeline9VolatilityFramework[5]–timelinerplugin[6]usedkernelobjects(process/thread/socket)eventlogsSpyEyebot(deadprocess)TCPconnectionestablishedbyexplorer.
exeCodeinjectionactivityAnalysisExample:DetectingCodeInjection10Detectingcodeinjection–VolatilityFrameworkmalfind–EnCaseEnScript[7]VadDump–MandiantRedline[8](GUIfront-endforMemoryze[9])ThetoolscheckprotectionflagofVirtualAddressDescriptorMandiantRedline(Memoryze)HBGaryResponderVolatilityFramework2.
0EnCaseEnScirptSupportedWindowsOSAllAllXP/Vista/7/2003/2008XP/7/2003/2008SupportedImageFormatRawRawRawCrashdumpHibernationRawCrashdumpSupportedCPUArchitectureIntelx86AMDx64Intelx86AMDx64Intelx86Intelx86AMDx64Extractingdeadprocess/closedconnectionNoNoYesYesNoteMalwareRiskIndex,MemD5DigitalDNA,codegraphingOpensource,richpluginsMultilingualsearch,EntropyComparisonofMemoryAnalysisTools11PREVIOUSWORKS:ANTIMEMORYFORENSICS12ShadowWalkerisproposedbySherriSparksandJamieButlertohidemaliciousmemoryregions–Installedpagefaulthandlermakesde-synchronizedDTLB/ITLBdataaccess->randomgarbagedataexecuteaccess->rootkitcodeMemoryacquisitiontoolscannotpreventShadowWalkerfromhidingmemorypages–ButAnalysistoolscandetecttheIDThooking13AntiAcquisitionMethods:ShadowWalker[10]Proofofconceptscript–killingspecifiedprocessesorpreventingdriverloadingswiththeaimofmemoryacquisitionfailureVeryeasytoimplement–Theevasionisalsoeasy(e.
g.
,randomname)–Preventingdriverloadingshasanimpactontherunningsystem14AntiAcquisitionMethods:MeterpreterAntiMemoryForensicsScript[11]Objectcarvingisonetechniquetoextractkernelobjectinformation–e.
g.
,processobject(_EPROCESS)PTFinder:Type/Sizein_DISPATCHER_HEADERVolatilityFramework:PoolTagin_POOL_HEADERBrendanDolan-Gavittetal.
warnedanattackercouldchangethevaluestohideaspecifiedobject[12]–Instead,theyproposedrobustsignaturescausingBSODorfunctionalityfailuresifthevaluesarechanged15AntiAnalysisMethod:AntiObjectCarvingmodifyingheadervaluesofcmd.
exeClosed-sourceanalysistoolscanfindthehiddenprocess–HowdotheyfinditOtherthanobjectcarving,thereareseveralkeyoperationsforanalyzingmemoryimage–TheoperationsarerobustLet'scheckit!
16AntiAnalysisMethod:AntiObjectCarving(Cont.
)MemoryzeHBGaryResponderPROPOSEDANTIANALYSISMETHOD17Researchedimplementationsofthreemajortools–VolatilityFramework2.
0–MandiantMemoryze2.
0–HBGaryResponderCommunityEdition2.
0Foundthreeoperationsexecutedinmemoryanalysisincludeafewunconsideredassumptions–Proposedmethodmodifiesone-byteofdatarelatedtotheoperationsThedataisdefinedas"AbortFactor"–Itcan'thidespecificobjects,butcanabortanalyses–NoimpactontherunningsystemNoBSOD,noerrorsforafewdaysto2weeks18AbstractofProposedMethodVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingkernelobjects–traversinglinkedlistsorbinarytrees–objectcarving19SensitiveThreeOperationsinMemoryAnalysisVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingkernelobjects–traversinglinkedlistsorbinarytrees–objectcarving20SensitiveThreeOperationsinMemoryAnalysisOSswitchesitscontextbyloadingDirectoryTableBase(DTB)ofeachprocess–DTBisstoredineachprocessobject(_EPROCESS)Initially,analysistoolsmustgetDTBvalueforkernelspaceTwoprocesseshavethekernelDTB–PsInitialSystemProcess(Systemprocess)–PsIdleProcess(Idleprocess)21VirtualAddressTranslationinKernelSpaceOSloadsDirectoryTableBase(Startphysicaladdressforaddresstranslation)intoControlRegister(CR3)x86AddressTranslation-HowPAEX86Workshttp://technet.
microsoft.
com/en-us/library/cc736309(WS.
10).
aspx22VirtualAddressTranslationinKernelSpace:ProcessObjectStructure_POOL_HEADER_OBJECT_HEADER_EPROCESS_KPROCESS_DISPATCHER_HEADERPoolTag:"Pro"TypeandSizeDTBImageFileName:"System"or"Idle"FlagsSearch_DISPATCHER_HEADERtoget_EPROCESSCheckwhethertheImageFileNameis"Idle"–IftheprocessisIdle,getDTBvaluein_KPROCESS23VirtualAddressTranslationinKernelSpace:VolatilityFramework_DISPATCHER_HEADER(e.
g.
,"x03x00x1bx00")ImageFileNameSearch"System"tofindImageFileNamein_EPROCESSofPsInitialSystemProcessValidatebyusing_DISPATCHER_HEADERinthe_KPROCESS–All_DISPATCHER_HEADERpatternsarechecked24VirtualAddressTranslationinKernelSpace:MandiantMemoryzeOSversion_DISPATCHER_HEADERByteSequenceXP32bit03001B00200332bit03001E00200364bit03002E00Vista32bit03002000Vista64bit03003000732bit03002600764bit03005800Validatebyusingthefollowingvalues–Flagsin_OBJECT_HEADERThedistancebetweenPoolTagand_EPROCESSiscalculatedaccordingtothevalue–PoolTagin_POOL_HEADERSearchPoolTagfrom_EPROCESSpositionandcheckwhetherthesearchhitoffsetisequaltothecalculateddistanceIfalldataisvalid,gettheDTBvalue25VirtualAddressTranslationinKernelSpace:MandiantMemoryze(Cont.
)Search_DISPATCHER_HEADERstoget_EPROCESSGetDTBvaluefromtheresultandvalidateitResponderseemstobeequippedwiththealgorithmguessingkernelDTB–IfDTBsofPsInitialSystemProcessandPsIdleProcessarenotfound,aguessedDTBvalueisused26VirtualAddressTranslationinKernelSpace:HBGaryResponder27VirtualAddressTranslationinKernelSpace:RelatedDataToolRelatedDataAbortFactorRemarksVolatilityFramework_DISPATCHER_HEADERXPsIdleProcessImageFileNamein_EPROCESSXMandiantMemoryze_DISPATCHER_HEADERXPsInitialSystemProcessPoolTagin_POOL_HEADERXFlagsin_OBJECT_HEADERXImageFileNamein_EPROCESSXHBGaryResponder_DISPATCHER_HEADERoriginalguessingalgorithmVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingKernelObjects–traversinglinkedlistsorbinarytrees–objectcarving28SensitiveThreeOperationsinMemoryAnalysisSizeanddefinitionofkerneldatastructuresdifferaccordingto–OSversion(e.
g.
,XPSP2/SP3,7SP0/SP1)–architecture(x86andx64)Allanalysistoolsguesstheversionusingdebugstructures29GuessingOSversionandArchitectureOSversion_EPROCESSsize(bytes)WindowsXPSP332bit0x260Windows7SP032bit0x2C0Windows7SP064bit0x4D0WindowsVistaSP232bit0x270WindowsVistaSP264bit0x3E830GuessingOSversionandArchitecture:DebugStructuresandKeyValues_KPCR_DBGKD_GET_VERSION64_KDDEBUGGER_DATA64KdVersionBlockDebuggerDataListHeaderCmNtCSDVersion_DBGKD_DEBUG_DATA_HEADER64OwnerTag:"KDBG"SizeKernBaseKernBasePrcbDataPsActiveProcessHeadPsLoadedModuleList_KPRCBCurrentThreadUsersmustspecifyOSversionandArchitecture–e.
g.
,--profile=WinXPSP2x86Iftheversionisunknown,imageinfocommandcanguessit–scan_DBGKD_DEBUG_DATA_HEADER64[13]31GuessingOSversionandArchitecture:VolatilityFrameworkOwnerTag:"KDBG"SizeSupposedlydetermineOSandarchitecturebasedon_DISPATCHER_HEADERValidatethembyusinganoffsetvalueofImageFileNamein_EPROCESS32GuessingOSversionandArchitecture:MandiantMemoryzeOSversionoffsetvalueofImageFileNameXP32bit0x174200332bitSP00x154200332bitSP1/SP20x164XP/200364bit0x268Vista32bit0x14CVista64bit0x238732bit0x16C7/200864bit0x2E0TrytotranslateavirtualaddressofThreadListHeadin_KPROCESS–Ifpossible,theOSversionandarchitecturearecorrectGetSPversionfromCmNtCSDVersionin_KDDEBUGGER_DATA6433GuessingOSversionandArchitecture:MandiantMemoryze(Cont.
)GetKernBasevalue–_DBGKD_GET_VERSION64or_KDDEBUGGER_DATA64ValidatethePEheadersignatures–DOSheader"MZ"andNTheader"PE"GetOSversion–OperatingSystemVersionsinOptionalHeadere.
g.
,Windows7–MajorOperatingSystemVersion=6–MinorOperatingSystemVersion=1Getmorespecificversion–TimeDataStampinFileheader34GuessingOSversionandArchitecture:HBGaryResponder35GuessingOSversionandArchitecture:RelatedDataToolRelatedDataAbortFactorRemarksVolatilityFramework_DBGKD_DEBUG_DATA_HEADER64XMandiantMemoryze_DISPATCHER_HEADERXPsInitialSystemProcessoffsetvalueofImageFileNameXThreadListHeadin_KPROCESSCmNtCSDVersionin_KDDEBUGGER_DATA64HBGaryResponderKernBasein_DBGKD_GET_VERSION64or_KDDEBUGGER_DATA64PEHeaderofWindowskernelPEheadersignatures"MZ"/"PE"OperatingSystemVersioninOptionalHeaderXTimeDataStampinFileHeaderVirtualaddresstranslationinkernelspaceGuessingOSversionandArchitectureGettingKernelObjects–traversinglinkedlistsorbinarytrees–objectcarving36SensitiveThreeOperationsinMemoryAnalysisTraversinglinkedlistsorbinarytrees–Generally,usespeciallead/rootaddressesPsActiveProcessHeadforprocesslistPsLoadedModuleListforkernelmodulelistVadRootforVirtualAddressDescriptortreeObjectcarving–Generally,usefixedvaluesinheaders_POOL_HEADER_DISPATCHER_HEADERMyresearchfocusedongetting_EPROCESS37GettingKernelObjectsProcesslististwo-waylink–Each_EPROCESSincludesActiveProcessLinks_LIST_ENTRY(FlinkandBlink)–PsActiveProcessHeadandPsInitialSystemProcessarebounduptogether38GettingKernelObjects:ProcessLinkedListPsActiveProcessHead_EPROCESS"System"_EPROCESS"smss.
exe"_EPROCESS"win32dd.
exe"FLINKBLINKFLINKBLINKFLINKBLINKFLINKBLINK.
.
.
.
.
.
.
.
.
Traversinglinkedlistsorbinarytrees–Search_DBGKD_DEBUG_DATA_HEADER64–getPsActiveProcessHeadin_KDDEBUGGER_DATA64Objectcarving–usePoolTagin_POOL_HEADER39GettingKernelObjects:VolatilityFrameworkExecutingKDBGScannerGetting_DBGKD_DEBUG_DATA_HEADER64(=_KDDEBUGGER_DATA64)addressObjectcarving–find_EPROCESSusingaddressvaluese.
g.
,–DTBis0x20-bytesaligned–(Peb&0x7ffd0000)==0x7ffd0000–(ActiveProcessLinks.
Flink&0x80000000)==0x80000000–similartorobustsignaturesproposedbyBrendanDolan-Gavittetal.
[12]40GettingKernelObjects:MandiantMemoryzeTraversinglinkedlistsorbinarytrees–getCurrentThreadin_KPRCB–get_EPROCESSfromthethreade.
g.
,ApcState.
Processin_KTHREAD(XP)–starttotraverseprocesslistfromthe_EPROCESS"System"stringiscomparedwithImageFileNameof_EPROCESS–foridentifyingPsActiveProcessHead–fordetectinghiddenprocess41GettingKernelObjects:HBGaryResponder42GettingKernelObjects:RelatedDataToolRelatedDataAbortFactorRemarksVolatilityFramework_DBGKD_DEBUG_DATA_HEADER64XPsActiveProcessHeadin_KDDEBUGGER_DATA64XPoolTagin_POOL_HEADERMandiantMemoryzeaddressvaluesin_EPROCESS(DTB,Peb,etc.
)HBGaryResponderCurrentThreadin_KPRCBPsInitialSystemProcess_EPROCESSpointerin_KTHREADImageFileNamein_EPROCESSX43AbortFactorsToolVirtualAddressTranslationinKernelSpaceGuessingOSversionandArchitectureGettingKernelObjectsVolatilityFramework2factors:_DISPATCHER_HEADERandImageFileName(PsIdleProcess)1factor:_DBGKD_DEBUG_DATA_HEADER642factors:_DBGKD_DEBUG_DATA_HEADER64andPsActiveProcessHeadMandiantMemoryze4factors:_DISPATCHER_HEADER,PoolTag,FlagsandImageFileName(PsInitialSystemProcess)2factors:_DISPATCHER_HEADERandoffsetvalueofImageFileName(PsInitialSystemProcess)NoneHBGaryResponderNone1factor:OperatingSystemVersionofkernelheader1factor:ImageFileName(PsInitialSystemProcess)Loadakerneldriverintox86XPVM–Thedrivermodifies1byteofthefollowingdataSizein_DISPATCHER_HEADERofPsIdleProcessPoolTagin_POOL_HEADERofPsInitialSystemProcessMajorOperatingSystemVersioninPEheaderofWindowskernelCheckthemodificationusingWinDbgAcquirethememoryimageusingLiveCloudKd[14]Analysisusingthreetools44DemousingPoCDriver(Video)IMPROVEMENTPLANS45GuessingbasedonaddressvaluesMinimumguessingSeparatingimplementationstogetkernelobjects46ImprovementPlansThemodificationofaddressvaluesoftencausesBSODorfunctionfailures–_EPROCESSobjectcarvingbyMemoryze–_KPCRobjectcarvingbyVolatilityFramework[15]47GuessingBasedonAddressValues_KPCRaddress==SelfPcrand_KPRCBaddress==PrcbSupportcrashdumpformat–Registervaluescannotbemodified48Minimumguessing(1)DataincrashdumpheaderExtractedfrom(Win32ddimplementation)AbortFactorDTBCR3registerOSversionnt!
NtBuildNumberXPAEenabledCR4registerPsActiveProcessHead_KDDEBUGGER_DATA64XPsLoadedModuleList_KDDEBUGGER_DATA64XSupportargumentpassingoptionsaboutDTBandOSversion–VolatilityFrameworksupportsthemspecifyOSversionbyusing"--profile"optionspecifyDTBvaluebyusing"--dtb"option49Minimumguessing(2)IfDTBvaluecannotbeacquired,displaytheresultminimally-extractedbyobjectcarving50SeparatingimplementationstogetkernelobjectsGettingtheseinformationdoesn'tneedDTBvalueWRAP-UP51Proposedantianalysismethodcanabortmemoryanalysistoolsbymodifyingonlyone-byte–ThemethodiseffectiveformemoryimagesofallOSversionsandarchitectures–Abouttheimpactontherunningsystem,longtermevaluationsmaybeneededIhope–Developersimprovetheimplementations–Usersfigureoutinternalsofmemoryanalysisanddealwithanalysiserrors52Wrap-up53Questions(twitter:@cci_forensics)PleasecompletetheSpeakerFeedbackSurveys!
[1]HBGaryFastDumpPro[2]EnCaseWinEn(build-intoolofEnCase)[3]MoonSolsWindowsMemoryToolkit[4]ReservedAddressSpaceinWindowsPhysicalMemory[5]VolatilityFramework[6]timelinerplugin[7]Update:MemoryForensicEnScript[8]MandiantRedline[9]MandiantMemoryze[10]"SHADOWWALKER"RaisingTheBarForRootkit[11]MeterpreterAntiMemoryForensics(Memoryze)Script[12]RobustSignaturesforKernelDataStructures[13]IdentifyingMemoryImages[14]YOURCLOUDISINMYPOCKET[15]FindingObjectRootsinVista(KPCR)54References
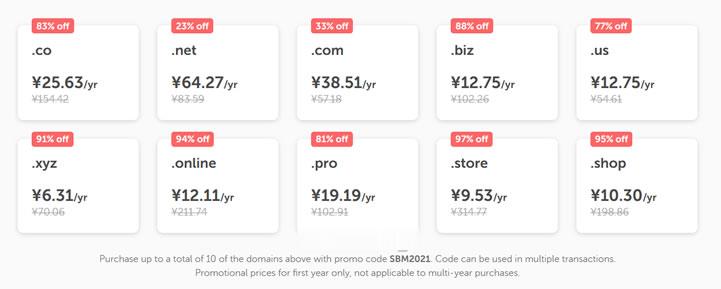
NameCheap优惠活动 新注册域名38元
今天上午有网友在群里聊到是不是有新注册域名的海外域名商家的优惠活动。如果我们并非一定要在国外注册域名的话,最近年中促销期间,国内的服务商优惠力度还是比较大的,以前我们可能较多选择海外域名商家注册域名在于海外商家便宜,如今这几年国内的商家价格也不贵的。比如在前一段时间有分享到几个商家的年中活动:1、DNSPOD域名欢购活动 - 提供域名抢购活动、DNS解析折扣、SSL证书活动2、难得再次关注新网商家...
Stablehost 美国主机商黑五虚拟主机四折
如今我们网友可能较多的会选择云服务器、VPS主机,对于虚拟主机的话可能很多人不会选择。但是我们有些外贸业务用途的建站项目还是会有选择虚拟主机的。今天看到的Stablehost 商家虚拟主机在黑五期间也有四折优惠,对于这个服务商而言不是特别的喜欢,虽然他们商家和我们熟悉的老鹰主机商有些类似,且在后来老鹰主机改版和方案后,Stablehost 商家也会跟随改版,但是性价比认为不如老鹰主机。这次黑色星期...

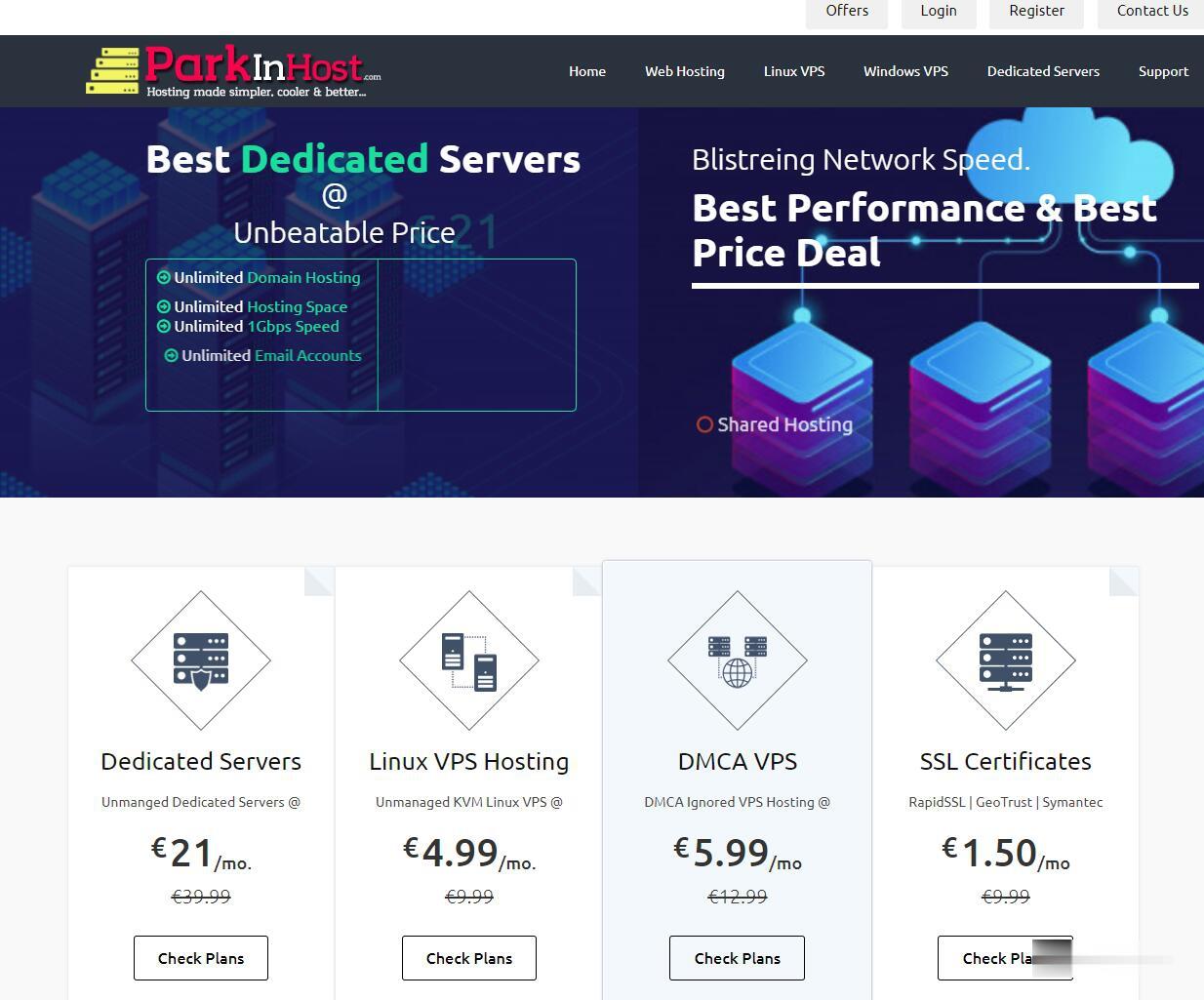
ParkinHost:俄罗斯离岸主机,抗投诉VPS,200Mbps带宽/莫斯科CN2线路/不限流量/无视DMCA/55折促销26.4欧元 /年起
外贸主机哪家好?抗投诉VPS哪家好?无视DMCA。ParkinHost今年还没有搞过促销,这次parkinhost俄罗斯机房上新服务器,母机采用2个E5-2680v3处理器、128G内存、RAID10硬盘、2Gbps上行线路。具体到VPS全部200Mbps带宽,除了最便宜的套餐限制流量之外,其他的全部是无限流量VPS。ParkinHost,成立于 2013 年,印度主机商,隶属于 DiggDigi...
spaceos为你推荐
-
哈利波特罗恩升级当爸哈利波特2为啥赫敏只抱哈利波特不抱罗恩。只是握手!!!这……johncusack谁知道《失控的陪审团》的电影内容是什么?约翰·库萨克在里面演的是什么角色?xyq.163.cbg.com梦幻CBG的网站是什么。百花百游百花百游的五滴自游进程同ip网站同IP网站9个越来越多,为什么?javmoo.com找下载JAV软件格式的网站789se.comhttp://gv789.com/index.php这个网站可信吗?是真的还是假的!www.se333se.com米奇网www.qvod333.com 看电影的效果好不?抓站工具大家在家用什么工具练站?怎么固定?面壁思过?在医院是站站立架m88.comwww.m88.com现在的官方网址是哪个啊 ?www.m88.com怎么样?