tierfilemarkets.com
filemarkets.com 时间:2021-03-21 阅读:()
October2015,IDC#259667MarketShareWorldwideSpecializedThreatAnalysisandProtectionMarketShares,2014:RapidlyEvolvingSecurityDefensesRobertWesterveltPeteLindstromRobAyoubElizabethCorrIDCMARKETSHAREFIGUREFIGURE1WorldwideSpecializedThreatAnalysisandProtection2014ShareSnapshotNote:2014Share(%),Growth(%),andRevenue($M)Source:IDC,20152015IDC#2596672EXECUTIVESUMMARYThespecializedthreatanalysisandprotection(STAP)marketcontinuedtogaintractionin2014withwidespreadadoptionofSaaSandon-premisessandboxesandarenewedfocusonemergingendpointsecuritytechnologies.
Organizationsarealsoincreasinglyevaluatingnetworkinspectionsolutionsdesignedtodetectattackermovementtosensitiveresources.
SignificantSTAPtrendsare:Vendorsconvertingproofofconcepts(POCs).
SecurityvendorsconvertedasignificantnumberofSTAPproofofconceptsin2014.
IDCestimatesthatthemarketin2014hadrevenueof$930million.
Itisforecasttogrowtoover$3billionby2019,withatotalmarketCAGRof27.
6%.
Identifyingattackermovement.
High-profileattacks,databreaches,andcriticalvulnerabilitiesin2013and2014droveinterestinNetFlowandotherproductsdesignedtodetectlateralmovementwithinacorporatenetwork.
FireEye,Lancope,IBM,andBit9-CarbonBlackwerethetop4securityvendorssellingSTAPsolutionsin2014.
Callingforincidentresponse(IR)support.
EarlyadoptersofSTAPsolutionssoughtincidentresponseexpertise,increasingdemandfordigitalforensicsspecialists,databreachsupport,andotherprofessionalservices.
Vendorsrespondedbyaddingorbolsteringtheirservicesofferingsin2014.
IDCbelievesthatemergingendpointsolutionsdesignedtodetectadvancedthreatswillgainmomentum.
Vendorsarecombiningmonitoringwithbehavioralanalyticswithothernon-signature-baseddetectioncapabilitiestoidentifyzerodays.
ThereissomeevidencethatendcustomersarebeginningtoshedstandardantivirusinfavorofsomeendpointSTAPsolutions.
TheSTAPmarketwillcontinuetoevolvewithestablishedsecurityvendorsaddingSTAPfeaturestotheirportfolioorganicallyoracquiringemergingSTAPsolutions.
In2014,PaloAltoNetworksacquiredIsraelistart-upCyveraforanestimated$200millionand,laterintheyear,introducedTraps,aSTAPendpointproductthatintegrateswithitsWildFirefilesandboxingservice.
CiscoSystemsacquiredThreatGRID,addingsuspiciousfileanalysissandboxingcapabilitiestoitsportfolio.
FireEyefurtherbuiltoutitsportfoliowiththeacquisitionofnPulseTechnologiestosupportforensicsandthreatremediationactivities.
ThisIDCstudyexaminesthecompetitivemarketforthisspecializedsecuritytechnology.
Itaimstoidentifythemarketleadersandsignificanttrendsthatwillimpactthebroadermarketforsecurityproductsandservices.
SecurityvendorproductsthatfitintotheSTAPmarketmustbesoldasadedicatedproductandpurchasedfromcustomerstospecificallyaddresstheproblemofidentifyingcustommalware.
"Thespecializedthreatanalysisandprotectionmarketisrapidlyevolving,withestablishedvendorsaddingSTAPofferingsthatcompeteagainstagrowingcadreofsecuritystart-ups.
Theinnovativesecuritytechnologiesinthismarketmodernizemanyoftheoutdatedapproachesthatattackersareeasilybypassingtoday.
OrganizationsareshowingsignificantinterestandadoptionofSTAPproductstoaddressthegrowingneedforadvancedthreatdetection.
"—RobertWestervelt,researchmanager,SecurityProducts,IDC2015IDC#2596673ADVICEFORTECHNOLOGYSUPPLIERSThespecializedthreatanalysisandprotectionmarketcontinuestobechallengingforvendors,buyers,andsaleschannelresellers.
ThecompetitivemarketcontinuestoevolvewithSTAPsecurityproductsoftenoverlappingavarietyofadjacentsecuritytechnologyareas.
SecurityvendorproductsthatfitintotheSTAPmarketmustbesoldasadedicatedproductandpurchasedfromcustomerstospecificallyaddresstheproblemofidentifyingcustommalware,sophisticatedattacktechniques,andotheractivityassociatedwithadvancedpersistentthreats.
Theproductsmustnotbesignaturebased.
BuyersareseekingtobolstertheirexistingsecurityinfrastructurebymakinganinvestmentinproductsdesignedtodetectadvancedthreatsfromeachofthethreeSTAPsubmarkets:endpoint,boundary,andinternalnetworkanalysis.
Somevendorsolutionsprovidefunctionalityfromeachofthesubmarkets,integratingemulationproductsdesignedtoanalyzesuspiciousfileswithbehavioralanalysistoidentifyfunctioncallsandsuspiciousfileactivityontheendpoint,andnetworkanalysistodetectattackerreconnaissanceactivityandlateralmovementwithinthenetwork.
EndpointSTAPproductsusebehavioralanalysisofmemoryandapplicationoperations.
Itprimarilyconsistsofanagentorsensorondevicesthatmonitorsystemprocessesandfilesforsignsofanomalousbehaviororattempttopreventsuspiciousfilesfromexecuting.
IDCanticipatesfutureconsolidationoftheendpointSTAPsubmarket,withtraditionalendpointsecurityvendorsaddingSTAPendpointcapabilitiestotheirplatforms.
BoundarySTAPproductsconsistmainlyofvirtualsandboxing/emulationandbehavioralanalysistechnologies.
Thesesafezonesareusedtodetonateandmonitorthebehaviorofsuspiciousfiles,whicharedesignedtoevadesignature-baseddefenses.
BuyershaveincreasinglypurchasedSaaS-basedsandboxingservices,buton-premisesandhybriddeploymentsarealsocommonwithenterprisecustomers.
InternalnetworkanalysisSTAPproductsmonitornetworkflowtodetectindicationsofattackerreconnaissanceactivity,malwaremovement,andbotnetormalwarecommandandcontrolactivity.
Productsshouldbeequippedtohelpresponderspinpointendpointinfectionsandinterruptcommandandcontrolcommunicationprovidecontexttoincidentresponders.
ThestrongestSTAPsolutionsappeartocomefromvendorsthathavecreatedstrongtechnologypartnerships,andIDChasdeterminedthatasecurityvendor'stechnologypartnerecosystemisbeingexaminedthoroughlyinproductevaluations.
Toremaincompetitive,securityvendorsshouldalsoconsiderthefollowingrecommendations:Strikekeydifferentiators:ProductevaluationsarebecomingasignificantchallengeforbuyersplanningtoadoptSTAPtechnology.
ChannelresellersarealsostrainedwhenattemptingtodetermineifaSTAPproductcanfitintheirportfoliowithoutconflictingwithtop-tiertechnologypartners.
Makeclearalldifferentiatingmanagementfeaturesandcapabilitiesagainstcompetitivesolutions.
Expanddeploymentoptions:Akeybuyingrequirementistheabilitytointegrateproductswithexistingsecurityinfrastructure.
ThisrequirementmayresultintheneedforfullSaaS,on-premises,oramixtureofSaaSandon-premisessolutions.
Whileusabilityandeffortlessdeploymentareadvantageous,buyersarealsochoosingSTAPsolutionswithflexibledeploymentmodels.
2015IDC#2596674Createservicesofferings:Ananalysisofearlyadopterbuyingbehaviorsfoundthatvendorservicesofferingsarenotaprimarybuyingrequirement;however,asecondinquirywithcustomersidentifiedasignificantneedforfollow-upservicesengagements.
Theservicesrequirementwaspromptedbyalackofroutinemaintenance,deficientincidentresponseprocesses,andpoorlyconfigureddeployments.
Developriskscoringmodels:BuyingtrendssuggesttheadditionofaconfigurableriskscoringmethodologytoassistrespondersinprioritizingalertscapturestheattentionofC-suiteexecutivesduringsalesengagements.
Despitethegrowingnumberofrisk-basedscoringcapabilitiesincorporatedintosecurityproducts,STAPvendorscanuseriskscoringasaproductdifferentiator.
Itcouldalsofosterthecomfortlevelrequiredtopromptorganizationstoembraceautomatedresponseandremediationfeatures.
MARKETSHARETheworldwideSTAPsecuritymarketroseto$930millionin2014,anincreaseof126.
3%from2013.
FireEyeremainstheSTAPmarketleader,with37.
9%shareofthemarketin2014.
Itsawitsshareofthemarketdecline5.
2%basedonadditionalmarketentrantsandwidespreadavailabilityofcompetingsandboxingsolutions.
AnotablecompetitorisPaloAltoNetworksandtherapidadoptionofitssubscription-basedWildFiresandboxingservicein2014.
Table1displays2011–2019worldwiderevenueandmarketsharefortheSTAPsecuritymarket.
Tables2–4display2014revenueandmarketsharesforthetopvendorsineachsubmarket.
STAPboundaryisthelargestmarketsegment,withFireEyecontinuingtobethesoledominatingvendor.
Sandboxingtechnologieshavequicklycometomarketfromnetworksecuritycompetitorsandsecuritystart-ups.
BoundarySTAPincludesproductsfromCheckPoint,Cyphort,iBoss,Fortinet,IntelSecurity,Proofpoint,Symantec,andothers.
Italsoincludesashareofsandboxingcomponentsthatexistwithinstandalonevendoradvancedthreatdefensesolutions(seeTable3).
STAPendpointisthefastest-growingmarketsegmentandonethatisquicklyevolvingasendpointsecurityvendors,includingSymantecandIntelSecurity,addendpointadvancedthreatdetectioncapabilitiestotheirplatformstomeettheirestablishedcustomerrequirements.
Lancopehasgainedsignificantadoptionofitsadvancedthreatdetectionsolution,leveragingitscloserelationshipwithCiscoSystems.
RSAandBlueCoatareeachtransformingtheirnetworkpacketcapturingappliances,whichhadbeenfocusedfordigitalforensicsinvestigations,intobreachdetectionandanalysisplatforms(seeTable4).
2015IDC#2596675TABLE1WorldwideSpecializedThreatAnalysisandProtectionRevenuebySegment,2011–2019($M)2011201220132014201520162017201820192014–2019CAGR(%)Boundary80.
6150.
5309.
0709.
81,119.
71,444.
31,653.
41,845.
32,001.
623.
0Endpoint9.
016.
039.
0101.
8212.
7353.
2494.
4618.
0716.
947.
8Internalnetworkanalysis21.
035.
063.
0118.
4202.
5287.
6342.
2386.
7421.
528.
9Total110.
6201.
5411.
0930.
01,535.
02,085.
02,490.
02,850.
03,140.
027.
6Source:IDC,2015TABLE2WorldwideSpecializedThreatAnalysisandProtectionRevenueofBoundarySegmentbyVendor,2014Revenue($M)FireEye353AhnLab25TrendMicro25Cisco25Fidelis23Websense23IBM20Lastline20PaloAltoNetworks17Other178.
8Source:IDC,20152015IDC#2596676TABLE3WorldwideSpecializedThreatAnalysisandProtectionRevenueofEndpointSegmentbyVendor,2014Revenue($M)Bit9-CB38.
0Cylance13.
0Bromium13.
0CrowdStrike12.
0Invincea12.
0Other13.
8Source:IDC,2015TABLE4WorldwideSpecializedThreatAnalysisandProtectionRevenueofInternalNetworkAnalysisSegmentbyVendor,2014Revenue($M)Lancope50.
0IBM15.
0Damballa15.
0BlueCoat13.
0RSA13.
0Other12.
4Source:IDC,20152015IDC#2596677WHOSHAPEDTHEYEARBit9acquiredCarbonBlackatthebeginningof2014andwasabletohighlighttheeffectivenessofitsmodernwhitelistingapproachwithCarbonBlack'sendpointforensicscapabilities.
CarbonBlackhadbeentremendouslysuccessfulwithitsapproachpriortotheacquisitiongainingadoptionwithSOCpersonnelandincidentresponseteamsforitsabilitytotakeacompleteinventoryofeveryfileonanendpointsystemandmonitorforsystemchanges.
Theacquisitionshiftedattentiononwaysorganizationscanmodernizetheirendpointsecuritysolutions.
FireEyegainedattentionwiththelaunchofitsEndpointSecurity(HXSeries)appliancein2014.
ThisproductusesMandiant'sproprietarytechnologyforincidentresponderstomonitorendpointsforthreatindicatorsandalertthesecurityoperationscenterteamaboutpossiblecompromisedendpoints.
EngineersareworkingonembeddingMandiant'sMIRfunctionalityintotheHXSeries,enablingresponderstorapidlyinvestigatepotentialthreats.
TheappliancecanbepurchasedseparatelyorbeintegratedwiththeFireEyeNXSeriesappliances.
PaloAltoNetworksacquiredMortaandCyverain2014toaddendpointvisibilitytoitsportfolio.
TheresultingendpointSTAPproductcalledTrapsisdesignedtoblockattackerexploitationtechniques.
TrapsintegrateswithWildFire,PaloAlto'sSaaS-basedsandboxingservice.
CiscoSystemsacquiredThreatGRID,addingasandboxforcloud-basedsuspiciousfileanalysis.
ThecompanyalsoshowedprogressinextendingtheAdvancedMalwareProtectioncomponentofitsSourcefireacquisitionasanadd-ontoitsASAUTMappliances.
LancopeleverageditsexistingpartnershipwithCiscoSystemstogaintractionintheSTAPmarketwithitsStealthWatchSystemforadvancedthreatdetection.
Lancopecompetesagainstothervendorsintheinternalnetworkanalysissubmarket,whichisdesignedtoidentifylateralmovementwithintrackingnetworkreconnaissance,internalmalwarepropagation,commandandcontroltraffic,anddataexfiltration.
ANoteonSymantecandIntelSecurityIntelSecurityismakinggainswithitsAdvancedThreatDefenseoffering,whichconsistsofastandaloneappliance,designedtointegratewithotherproductsinitsportfolio.
IntelSecurityusesalocalblacklisttodetectknownmalwareandavirtualsandboxenvironmentforsuspiciousfileanalysis.
ItconnectstoIntelSecurity'scloud-basedGlobalThreatIntelligenceforfurtherprotection.
Symantecannouncedthatitwouldsplitintoseparatesecurityandinformationmanagementbusinessesin2014.
ThecompanyalsoannouncedplanstoinvestinitsportfolioofsecurityproductsandentertheSTAPmarketwithanAdvancedThreatProtectionproductthatintegratesitsexistingemail,networking,andendpointsolutionswithfileinspectiontechnologycalledSymantecCynic,acloud-basedsandboxenvironmentforfileinspection.
SymantecalsoleveragesatechnologyitcallsSynapsetocorrelateeventinformationbetweenthenetwork,endpoints,andemailtoprovidecontexttoalertsforincidentresponders.
MARKETCONTEXTTheSTAPmarketgainedconsiderabletractionin2014asendusersincreasedsecurityspendingtostemtheever-increasingnumberofdatabreaches.
TheTargetbreachinparticularraisedthestakesforsecurityaccountabilityastheCEOwasforcedtoresigninpartasaresultofthemassivedata2015IDC#2596678breach.
STAPproductsarerepresentingthefirstsignificantshiftinthesecuritystackinsometime,andIDCpredictsthatorganizationswillcontinuetodeploytheseproductseitherthroughon-premisesdevices,throughendpointclients,orviathecloud.
ThethreeSTAPsubsegmentsthatIDCistracking—boundary,internalnetwork,andendpoint—havestrongenterpriseinterestandadoption.
However,thesereasonsvarybasedoneachsegment:Boundary.
TheinterestinboundarydeviceshasbeenpromptedprimarilybythesuccessofFireEyeandotherstodeliversandboxingandotheridentificationtechniquesonthenetwork.
Manysecurityadministratorsareverycomfortablewithaddingsecuritydevicestothenetworkandasaresultthesedevicesfiteasilyintotheday-to-daysecurityoperationsfunction.
Internalnetwork.
InternalnetworkSTAPproductsareprimarilyfocusedonbotnetdetectionanddeterminingifmalwarehasinfectedthenetwork.
Insteadoftryingtoevaluatethetrafficflowingthroughthenetworkboundaries,internalnetworkSTAPproductsrelyonuserbehavior,flowtraffic,andDNStraffictodeterminewhetherthereismaliciousbehavioronthenetwork.
OnekeyadvantagetoutedbyinternalnetworkSTAPproductsoverboundaryproductsisareductionintheamountoffalsepositives.
Endpoint.
EndpointSTAPproductsarebeingheraldedasthenextgenerationofendpointsecurity.
Asenterpriseshavebecomemoredisillusionedwithlegacyendpointsecurityproducts,theinterestinsolutionsthatarefasterandmoreaccuratehasincreased.
EndpointSTAPvendorsareapproachingendpointsecurityusingawidevarietyofmethodstoimprovethedetectionandpreventioncapabilitiesofmalwareontheendpoint.
OtherendpointSTAPproductsaremorefocusedonanalyticscollectionandvisibilityintotheendpointandthencoordinatethatdatawithnetwork-basedproducts.
IDCdoesnotbelievethatanysingleapproachorproductwillsolveanorganization'ssecuritychallenges,butbyusingacombinationofSTAPproductswithtraditionalsecurityproducts,thatmanyblindspotscanbeeliminated.
SignificantMarketDevelopmentsSecurityvendorFireEye'scontinuedsuccesshasresultedinaninfluxofadvancedthreatdefenseofferingsthatusevirtualsandboxestoanalyzesuspiciousfilesandidentifyadvancedthreats.
Thesolutions,whichfirstappealedtolargeenterprises,haveexperiencedgrowthbycapturingabroadersegmentofthemarket,whichquicklyembracedcloud-basedsandboxingservices.
Avarietyofpure-playvendorswithsandboxingofferingscontinuetomaketheboundarysubmarketextremelylargecomparedwithendpointandinternalnetworkanalysis.
Bit9'sacquisitionofCarbonBlackhashelpedfuelinterestinmodernizingendpointdefenses,whichhavebeenrelyingheavilyonsignature-basedtechnologytodetectmalware.
Newconceptsarebeingintroducedthatincorporateendpointagentorsensortechnologytoincreasevisibilityandgiveincidentrespondersmorecontextintoalertsandcontroloverinfectedsystems.
EndpointSTAPisrapidlyevolving.
Theattentiongiventopure-playvendorshaspromptedestablishedsecurityvendorstoaddsimilarspecializedthreatanalysisandprotectioncapabilities.
Therootofmanyoftheseemergingtechnologiesisinhost-basedintrusionpreventionanddigitalforensicscapabilitiesthatidentifythreatsinunderlyingsystemmemory,abnormalapplicationfunctioncalls,andothersignsofunusualsystembehavior.
IDCisawareofAccessData,FireEyeMIR,GuidanceSoftwareEncase,RSAECAT,andotherforensicstoolsthathelprespondersgainvisibilitywhileinvestigatingthescopeofaninfection.
IDC2015IDC#2596679analystsexaminetheseproductscloselytodeterminewhetherthereisreal-timemonitoringandalertingcapabilitiesandthecustomerrequirementsandusecasesthattheproductsfulfill.
METHODOLOGYThisIDCsoftwaremarketsizingandforecastispresentedintermsofpackagedsoftwareandappliancerevenue.
IDCusesthetermpackagedsoftwaretodistinguishcommerciallyavailablesoftwarefromcustomsoftware,nottoimplythatthesoftwaremustbeshrink-wrappedorotherwiseprovidedviaphysicalmedia.
Packagedsoftwareisprogramsorcodesetsofanytypecommerciallyavailablethroughsale,lease,orrental,orasaservice.
Packagedsoftwarerevenuetypicallyincludesfeesforinitialandcontinuedright-to-usepackagedsoftwarelicenses.
Thesefeesmayinclude,aspartofthelicensecontract,accesstoproductsupportand/orotherservicesthatareinseparablefromtheright-to-uselicensefeestructure,orthissupportmaybepricedseparately.
Upgradesmaybeincludedinthecontinuingrightofuseormaybepricedseparately.
AllofthesearecountedbyIDCaspackagedsoftwarerevenue.
Appliancesaredefinedasacombinationofhardware,operatingenvironment,andapplicationsoftwarewheretheyareprovidedasasingleproduct.
Packagedsoftwarerevenueexcludesservicerevenuederivedfromtraining,consulting,andsystemsintegrationthatisseparate(orunbundled)fromtheright-to-uselicensebutdoesincludetheimplicitvalueoftheproductincludedinaservicethatofferssoftwarefunctionalitybyadifferentpricingscheme.
Itisthetotalproductrevenuethatisfurtherallocatedtomarkets,geographicareas,andoperatingenvironments.
Themarketforecastandanalysismethodologyincorporatesinformationfromfivedifferentbutinterrelatedsources,asfollows:Reportedandobservedtrendsandfinancialactivity.
Thisstudyincorporatesreportedandobservedtrendsandfinancialactivityin2014asoftheendofSeptember2015.
IDC'sSoftwareCensusinterviews.
IDCinterviewsallsignificantmarketparticipantstodetermineproductrevenue,revenuedemographics,pricing,andotherrelevantinformation.
Productbriefings,pressreleases,andotherpubliclyavailableinformation.
IDC'ssoftwareanalystsaroundtheworldmeetwithhundredsofsoftwarevendorseachyear.
Thesebriefingsprovideanopportunitytoreviewcurrentandfuturebusinessandproductstrategies,revenue,shipments,customerbases,targetmarkets,andotherkeyproductandcompetitiveinformation.
Vendorfinancialstatementsandrelatedfilings.
Althoughmanysoftwarevendorsareprivatelyheldandchoosetolimitfinancialdisclosures,informationfrompubliclyheldcompaniesprovidesasignificantbenchmarkforassessinginformalmarketestimatesfromprivatecompanies.
IDCalsobuildsdetailedinformationrelatedtoprivatecompaniesthroughin-depthanalystrelationshipsandmaintainsanextensivelibraryoffinancialandcorporateinformationfocusedontheITindustry.
Wefurthermaintaindetailedrevenuebyproductareamodelsonmorethan1,000worldwidevendors.
IDCdemand-sideresearch.
Thisincludesthousandsofinterviewswithbusinessusersofsoftwaresolutionsannuallyandprovidesapowerfulfifthperspectiveforassessingcompetitiveperformanceandmarketdynamics.
IDC'suserstrategydatabasesofferacompellingandconsistenttime-seriesviewofindustrytrendsanddevelopments.
Directconversationswithtechnologybuyersprovideaninvaluablecomplementtothebroadersurvey-basedresults.
2015IDC#25966710Ultimately,thedatapresentedinthisstudyrepresentsIDC'sbestestimatesbasedonthesedatasourcesaswellasreportedandobservedactivitybyvendorsandfurthermodelingofdatathatwebelievetobetruetofillinanyinformationgaps.
ThedatainthisstudyisderivedfromallthesesourcesandenteredintoIDC'sSoftwareMarketForecasterdatabase,whichisthenupdatedonacontinuousbasisasnewinformationregardingsoftwarevendorrevenuebecomesavailable.
Note:Allnumbersinthisdocumentmaynotbeexactduetorounding.
MARKETDEFINITIONThespecializedthreatanalysisandprotectionmarketoverlapstheendpoint,messaging,network,andWebfunctionalmarkets.
Theproductshelpprotectenterprisesfromnewmalwareattacksthatcannotbedetectedbytraditionalsignature-basedtechniques.
TheSTAPproductsuseavarietyofnon-signature-basedprotectionmethodsincluding,butnotlimitedto,sandboxing,behavioralanalysis,fileintegritymonitoring,telemetricheuristics,containerization,netflowanalysis,andthreatintelligence,whichcandetectamalwareattackorcompromisebyidentifyingattackeractivityorsubtlesystemprocesschanges.
Someoftheproductsonlydetectandalert,whileothersmaycontainmalwaretopreventitfromcausingdamage.
Althoughthesefeaturesmayappearinotherproducts,thiscategoryisonlyfordedicatedSTAPsolutions.
TheSTAPmarketismadeupofdistinguishableproductsasopposedtoembeddedfeatureswithinaproduct.
Theabilitytofindandpreventadvancedmalwareultimatelyrequiresdedicatedactivities,andinthisway,itispossibletomeasuretheextentthatenterprisesareconsciouslytakingactionstodealwithadvancedmalware.
TheSTAPmarketisacompetitivemarketthatoverlapsotherlogicalsecurityproductsmarkets(e.
g.
,IAM,network,endpoint,messaging,Web,SVM,and"other"securityproducts).
TheSTAPmarketmustbereportedseparatelyand,furthermore,notaddedtothesevenlogicalsecurityproductsmarkets,otherwisethetotalsecurityproductsmarketfigurewillbeincorrect.
RELATEDRESEARCHIDC'sForecastScenarioAssumptionsfortheICTMarketsandHistoricalMarketValuesandExchangeRates,Version3,2015(IDC#259115,September2015)WorldwideSpecializedThreatAnalysisandProtectionForecast,2015–2019:DefendingAgainsttheUnknown(IDC#256354,May2015)MarketAnalysisPerspective:WorldwideSecurityProducts,2014(IDC#252908,December2014)WorldwideITSecurityProducts2014–2018Forecastand2013VendorShares:ComprehensiveSecurityProductReview(IDC#253371,December2014)IDC'sWorldwideSecurityProductsTaxonomy,2014(IDC#250802,September2014)WorldwideSpecializedThreatAnalysisandProtection2013–2017Forecastand2012VendorShares(IDC#242346,August2013)AboutIDCInternationalDataCorporation(IDC)isthepremierglobalproviderofmarketintelligence,advisoryservices,andeventsfortheinformationtechnology,telecommunicationsandconsumertechnologymarkets.
IDChelpsITprofessionals,businessexecutives,andtheinvestmentcommunitymakefact-baseddecisionsontechnologypurchasesandbusinessstrategy.
Morethan1,100IDCanalystsprovideglobal,regional,andlocalexpertiseontechnologyandindustryopportunitiesandtrendsinover110countriesworldwide.
For50years,IDChasprovidedstrategicinsightstohelpourclientsachievetheirkeybusinessobjectives.
IDCisasubsidiaryofIDG,theworld'sleadingtechnologymedia,research,andeventscompany.
GlobalHeadquarters5SpeenStreetFramingham,MA01701USA508.
872.
8200Twitter:@IDCidc-insights-community.
comwww.
idc.
comCopyrightNoticeThisIDCresearchdocumentwaspublishedaspartofanIDCcontinuousintelligenceservice,providingwrittenresearch,analystinteractions,telebriefings,andconferences.
Visitwww.
idc.
comtolearnmoreaboutIDCsubscriptionandconsultingservices.
ToviewalistofIDCofficesworldwide,visitwww.
idc.
com/offices.
PleasecontacttheIDCHotlineat800.
343.
4952,ext.
7988(or+1.
508.
988.
7988)orsales@idc.
comforinformationonapplyingthepriceofthisdocumenttowardthepurchaseofanIDCserviceorforinformationonadditionalcopiesorWebrights.
[trademark]Copyright2015IDC.
Reproductionisforbiddenunlessauthorized.
Allrightsreserved.
Organizationsarealsoincreasinglyevaluatingnetworkinspectionsolutionsdesignedtodetectattackermovementtosensitiveresources.
SignificantSTAPtrendsare:Vendorsconvertingproofofconcepts(POCs).
SecurityvendorsconvertedasignificantnumberofSTAPproofofconceptsin2014.
IDCestimatesthatthemarketin2014hadrevenueof$930million.
Itisforecasttogrowtoover$3billionby2019,withatotalmarketCAGRof27.
6%.
Identifyingattackermovement.
High-profileattacks,databreaches,andcriticalvulnerabilitiesin2013and2014droveinterestinNetFlowandotherproductsdesignedtodetectlateralmovementwithinacorporatenetwork.
FireEye,Lancope,IBM,andBit9-CarbonBlackwerethetop4securityvendorssellingSTAPsolutionsin2014.
Callingforincidentresponse(IR)support.
EarlyadoptersofSTAPsolutionssoughtincidentresponseexpertise,increasingdemandfordigitalforensicsspecialists,databreachsupport,andotherprofessionalservices.
Vendorsrespondedbyaddingorbolsteringtheirservicesofferingsin2014.
IDCbelievesthatemergingendpointsolutionsdesignedtodetectadvancedthreatswillgainmomentum.
Vendorsarecombiningmonitoringwithbehavioralanalyticswithothernon-signature-baseddetectioncapabilitiestoidentifyzerodays.
ThereissomeevidencethatendcustomersarebeginningtoshedstandardantivirusinfavorofsomeendpointSTAPsolutions.
TheSTAPmarketwillcontinuetoevolvewithestablishedsecurityvendorsaddingSTAPfeaturestotheirportfolioorganicallyoracquiringemergingSTAPsolutions.
In2014,PaloAltoNetworksacquiredIsraelistart-upCyveraforanestimated$200millionand,laterintheyear,introducedTraps,aSTAPendpointproductthatintegrateswithitsWildFirefilesandboxingservice.
CiscoSystemsacquiredThreatGRID,addingsuspiciousfileanalysissandboxingcapabilitiestoitsportfolio.
FireEyefurtherbuiltoutitsportfoliowiththeacquisitionofnPulseTechnologiestosupportforensicsandthreatremediationactivities.
ThisIDCstudyexaminesthecompetitivemarketforthisspecializedsecuritytechnology.
Itaimstoidentifythemarketleadersandsignificanttrendsthatwillimpactthebroadermarketforsecurityproductsandservices.
SecurityvendorproductsthatfitintotheSTAPmarketmustbesoldasadedicatedproductandpurchasedfromcustomerstospecificallyaddresstheproblemofidentifyingcustommalware.
"Thespecializedthreatanalysisandprotectionmarketisrapidlyevolving,withestablishedvendorsaddingSTAPofferingsthatcompeteagainstagrowingcadreofsecuritystart-ups.
Theinnovativesecuritytechnologiesinthismarketmodernizemanyoftheoutdatedapproachesthatattackersareeasilybypassingtoday.
OrganizationsareshowingsignificantinterestandadoptionofSTAPproductstoaddressthegrowingneedforadvancedthreatdetection.
"—RobertWestervelt,researchmanager,SecurityProducts,IDC2015IDC#2596673ADVICEFORTECHNOLOGYSUPPLIERSThespecializedthreatanalysisandprotectionmarketcontinuestobechallengingforvendors,buyers,andsaleschannelresellers.
ThecompetitivemarketcontinuestoevolvewithSTAPsecurityproductsoftenoverlappingavarietyofadjacentsecuritytechnologyareas.
SecurityvendorproductsthatfitintotheSTAPmarketmustbesoldasadedicatedproductandpurchasedfromcustomerstospecificallyaddresstheproblemofidentifyingcustommalware,sophisticatedattacktechniques,andotheractivityassociatedwithadvancedpersistentthreats.
Theproductsmustnotbesignaturebased.
BuyersareseekingtobolstertheirexistingsecurityinfrastructurebymakinganinvestmentinproductsdesignedtodetectadvancedthreatsfromeachofthethreeSTAPsubmarkets:endpoint,boundary,andinternalnetworkanalysis.
Somevendorsolutionsprovidefunctionalityfromeachofthesubmarkets,integratingemulationproductsdesignedtoanalyzesuspiciousfileswithbehavioralanalysistoidentifyfunctioncallsandsuspiciousfileactivityontheendpoint,andnetworkanalysistodetectattackerreconnaissanceactivityandlateralmovementwithinthenetwork.
EndpointSTAPproductsusebehavioralanalysisofmemoryandapplicationoperations.
Itprimarilyconsistsofanagentorsensorondevicesthatmonitorsystemprocessesandfilesforsignsofanomalousbehaviororattempttopreventsuspiciousfilesfromexecuting.
IDCanticipatesfutureconsolidationoftheendpointSTAPsubmarket,withtraditionalendpointsecurityvendorsaddingSTAPendpointcapabilitiestotheirplatforms.
BoundarySTAPproductsconsistmainlyofvirtualsandboxing/emulationandbehavioralanalysistechnologies.
Thesesafezonesareusedtodetonateandmonitorthebehaviorofsuspiciousfiles,whicharedesignedtoevadesignature-baseddefenses.
BuyershaveincreasinglypurchasedSaaS-basedsandboxingservices,buton-premisesandhybriddeploymentsarealsocommonwithenterprisecustomers.
InternalnetworkanalysisSTAPproductsmonitornetworkflowtodetectindicationsofattackerreconnaissanceactivity,malwaremovement,andbotnetormalwarecommandandcontrolactivity.
Productsshouldbeequippedtohelpresponderspinpointendpointinfectionsandinterruptcommandandcontrolcommunicationprovidecontexttoincidentresponders.
ThestrongestSTAPsolutionsappeartocomefromvendorsthathavecreatedstrongtechnologypartnerships,andIDChasdeterminedthatasecurityvendor'stechnologypartnerecosystemisbeingexaminedthoroughlyinproductevaluations.
Toremaincompetitive,securityvendorsshouldalsoconsiderthefollowingrecommendations:Strikekeydifferentiators:ProductevaluationsarebecomingasignificantchallengeforbuyersplanningtoadoptSTAPtechnology.
ChannelresellersarealsostrainedwhenattemptingtodetermineifaSTAPproductcanfitintheirportfoliowithoutconflictingwithtop-tiertechnologypartners.
Makeclearalldifferentiatingmanagementfeaturesandcapabilitiesagainstcompetitivesolutions.
Expanddeploymentoptions:Akeybuyingrequirementistheabilitytointegrateproductswithexistingsecurityinfrastructure.
ThisrequirementmayresultintheneedforfullSaaS,on-premises,oramixtureofSaaSandon-premisessolutions.
Whileusabilityandeffortlessdeploymentareadvantageous,buyersarealsochoosingSTAPsolutionswithflexibledeploymentmodels.
2015IDC#2596674Createservicesofferings:Ananalysisofearlyadopterbuyingbehaviorsfoundthatvendorservicesofferingsarenotaprimarybuyingrequirement;however,asecondinquirywithcustomersidentifiedasignificantneedforfollow-upservicesengagements.
Theservicesrequirementwaspromptedbyalackofroutinemaintenance,deficientincidentresponseprocesses,andpoorlyconfigureddeployments.
Developriskscoringmodels:BuyingtrendssuggesttheadditionofaconfigurableriskscoringmethodologytoassistrespondersinprioritizingalertscapturestheattentionofC-suiteexecutivesduringsalesengagements.
Despitethegrowingnumberofrisk-basedscoringcapabilitiesincorporatedintosecurityproducts,STAPvendorscanuseriskscoringasaproductdifferentiator.
Itcouldalsofosterthecomfortlevelrequiredtopromptorganizationstoembraceautomatedresponseandremediationfeatures.
MARKETSHARETheworldwideSTAPsecuritymarketroseto$930millionin2014,anincreaseof126.
3%from2013.
FireEyeremainstheSTAPmarketleader,with37.
9%shareofthemarketin2014.
Itsawitsshareofthemarketdecline5.
2%basedonadditionalmarketentrantsandwidespreadavailabilityofcompetingsandboxingsolutions.
AnotablecompetitorisPaloAltoNetworksandtherapidadoptionofitssubscription-basedWildFiresandboxingservicein2014.
Table1displays2011–2019worldwiderevenueandmarketsharefortheSTAPsecuritymarket.
Tables2–4display2014revenueandmarketsharesforthetopvendorsineachsubmarket.
STAPboundaryisthelargestmarketsegment,withFireEyecontinuingtobethesoledominatingvendor.
Sandboxingtechnologieshavequicklycometomarketfromnetworksecuritycompetitorsandsecuritystart-ups.
BoundarySTAPincludesproductsfromCheckPoint,Cyphort,iBoss,Fortinet,IntelSecurity,Proofpoint,Symantec,andothers.
Italsoincludesashareofsandboxingcomponentsthatexistwithinstandalonevendoradvancedthreatdefensesolutions(seeTable3).
STAPendpointisthefastest-growingmarketsegmentandonethatisquicklyevolvingasendpointsecurityvendors,includingSymantecandIntelSecurity,addendpointadvancedthreatdetectioncapabilitiestotheirplatformstomeettheirestablishedcustomerrequirements.
Lancopehasgainedsignificantadoptionofitsadvancedthreatdetectionsolution,leveragingitscloserelationshipwithCiscoSystems.
RSAandBlueCoatareeachtransformingtheirnetworkpacketcapturingappliances,whichhadbeenfocusedfordigitalforensicsinvestigations,intobreachdetectionandanalysisplatforms(seeTable4).
2015IDC#2596675TABLE1WorldwideSpecializedThreatAnalysisandProtectionRevenuebySegment,2011–2019($M)2011201220132014201520162017201820192014–2019CAGR(%)Boundary80.
6150.
5309.
0709.
81,119.
71,444.
31,653.
41,845.
32,001.
623.
0Endpoint9.
016.
039.
0101.
8212.
7353.
2494.
4618.
0716.
947.
8Internalnetworkanalysis21.
035.
063.
0118.
4202.
5287.
6342.
2386.
7421.
528.
9Total110.
6201.
5411.
0930.
01,535.
02,085.
02,490.
02,850.
03,140.
027.
6Source:IDC,2015TABLE2WorldwideSpecializedThreatAnalysisandProtectionRevenueofBoundarySegmentbyVendor,2014Revenue($M)FireEye353AhnLab25TrendMicro25Cisco25Fidelis23Websense23IBM20Lastline20PaloAltoNetworks17Other178.
8Source:IDC,20152015IDC#2596676TABLE3WorldwideSpecializedThreatAnalysisandProtectionRevenueofEndpointSegmentbyVendor,2014Revenue($M)Bit9-CB38.
0Cylance13.
0Bromium13.
0CrowdStrike12.
0Invincea12.
0Other13.
8Source:IDC,2015TABLE4WorldwideSpecializedThreatAnalysisandProtectionRevenueofInternalNetworkAnalysisSegmentbyVendor,2014Revenue($M)Lancope50.
0IBM15.
0Damballa15.
0BlueCoat13.
0RSA13.
0Other12.
4Source:IDC,20152015IDC#2596677WHOSHAPEDTHEYEARBit9acquiredCarbonBlackatthebeginningof2014andwasabletohighlighttheeffectivenessofitsmodernwhitelistingapproachwithCarbonBlack'sendpointforensicscapabilities.
CarbonBlackhadbeentremendouslysuccessfulwithitsapproachpriortotheacquisitiongainingadoptionwithSOCpersonnelandincidentresponseteamsforitsabilitytotakeacompleteinventoryofeveryfileonanendpointsystemandmonitorforsystemchanges.
Theacquisitionshiftedattentiononwaysorganizationscanmodernizetheirendpointsecuritysolutions.
FireEyegainedattentionwiththelaunchofitsEndpointSecurity(HXSeries)appliancein2014.
ThisproductusesMandiant'sproprietarytechnologyforincidentresponderstomonitorendpointsforthreatindicatorsandalertthesecurityoperationscenterteamaboutpossiblecompromisedendpoints.
EngineersareworkingonembeddingMandiant'sMIRfunctionalityintotheHXSeries,enablingresponderstorapidlyinvestigatepotentialthreats.
TheappliancecanbepurchasedseparatelyorbeintegratedwiththeFireEyeNXSeriesappliances.
PaloAltoNetworksacquiredMortaandCyverain2014toaddendpointvisibilitytoitsportfolio.
TheresultingendpointSTAPproductcalledTrapsisdesignedtoblockattackerexploitationtechniques.
TrapsintegrateswithWildFire,PaloAlto'sSaaS-basedsandboxingservice.
CiscoSystemsacquiredThreatGRID,addingasandboxforcloud-basedsuspiciousfileanalysis.
ThecompanyalsoshowedprogressinextendingtheAdvancedMalwareProtectioncomponentofitsSourcefireacquisitionasanadd-ontoitsASAUTMappliances.
LancopeleverageditsexistingpartnershipwithCiscoSystemstogaintractionintheSTAPmarketwithitsStealthWatchSystemforadvancedthreatdetection.
Lancopecompetesagainstothervendorsintheinternalnetworkanalysissubmarket,whichisdesignedtoidentifylateralmovementwithintrackingnetworkreconnaissance,internalmalwarepropagation,commandandcontroltraffic,anddataexfiltration.
ANoteonSymantecandIntelSecurityIntelSecurityismakinggainswithitsAdvancedThreatDefenseoffering,whichconsistsofastandaloneappliance,designedtointegratewithotherproductsinitsportfolio.
IntelSecurityusesalocalblacklisttodetectknownmalwareandavirtualsandboxenvironmentforsuspiciousfileanalysis.
ItconnectstoIntelSecurity'scloud-basedGlobalThreatIntelligenceforfurtherprotection.
Symantecannouncedthatitwouldsplitintoseparatesecurityandinformationmanagementbusinessesin2014.
ThecompanyalsoannouncedplanstoinvestinitsportfolioofsecurityproductsandentertheSTAPmarketwithanAdvancedThreatProtectionproductthatintegratesitsexistingemail,networking,andendpointsolutionswithfileinspectiontechnologycalledSymantecCynic,acloud-basedsandboxenvironmentforfileinspection.
SymantecalsoleveragesatechnologyitcallsSynapsetocorrelateeventinformationbetweenthenetwork,endpoints,andemailtoprovidecontexttoalertsforincidentresponders.
MARKETCONTEXTTheSTAPmarketgainedconsiderabletractionin2014asendusersincreasedsecurityspendingtostemtheever-increasingnumberofdatabreaches.
TheTargetbreachinparticularraisedthestakesforsecurityaccountabilityastheCEOwasforcedtoresigninpartasaresultofthemassivedata2015IDC#2596678breach.
STAPproductsarerepresentingthefirstsignificantshiftinthesecuritystackinsometime,andIDCpredictsthatorganizationswillcontinuetodeploytheseproductseitherthroughon-premisesdevices,throughendpointclients,orviathecloud.
ThethreeSTAPsubsegmentsthatIDCistracking—boundary,internalnetwork,andendpoint—havestrongenterpriseinterestandadoption.
However,thesereasonsvarybasedoneachsegment:Boundary.
TheinterestinboundarydeviceshasbeenpromptedprimarilybythesuccessofFireEyeandotherstodeliversandboxingandotheridentificationtechniquesonthenetwork.
Manysecurityadministratorsareverycomfortablewithaddingsecuritydevicestothenetworkandasaresultthesedevicesfiteasilyintotheday-to-daysecurityoperationsfunction.
Internalnetwork.
InternalnetworkSTAPproductsareprimarilyfocusedonbotnetdetectionanddeterminingifmalwarehasinfectedthenetwork.
Insteadoftryingtoevaluatethetrafficflowingthroughthenetworkboundaries,internalnetworkSTAPproductsrelyonuserbehavior,flowtraffic,andDNStraffictodeterminewhetherthereismaliciousbehavioronthenetwork.
OnekeyadvantagetoutedbyinternalnetworkSTAPproductsoverboundaryproductsisareductionintheamountoffalsepositives.
Endpoint.
EndpointSTAPproductsarebeingheraldedasthenextgenerationofendpointsecurity.
Asenterpriseshavebecomemoredisillusionedwithlegacyendpointsecurityproducts,theinterestinsolutionsthatarefasterandmoreaccuratehasincreased.
EndpointSTAPvendorsareapproachingendpointsecurityusingawidevarietyofmethodstoimprovethedetectionandpreventioncapabilitiesofmalwareontheendpoint.
OtherendpointSTAPproductsaremorefocusedonanalyticscollectionandvisibilityintotheendpointandthencoordinatethatdatawithnetwork-basedproducts.
IDCdoesnotbelievethatanysingleapproachorproductwillsolveanorganization'ssecuritychallenges,butbyusingacombinationofSTAPproductswithtraditionalsecurityproducts,thatmanyblindspotscanbeeliminated.
SignificantMarketDevelopmentsSecurityvendorFireEye'scontinuedsuccesshasresultedinaninfluxofadvancedthreatdefenseofferingsthatusevirtualsandboxestoanalyzesuspiciousfilesandidentifyadvancedthreats.
Thesolutions,whichfirstappealedtolargeenterprises,haveexperiencedgrowthbycapturingabroadersegmentofthemarket,whichquicklyembracedcloud-basedsandboxingservices.
Avarietyofpure-playvendorswithsandboxingofferingscontinuetomaketheboundarysubmarketextremelylargecomparedwithendpointandinternalnetworkanalysis.
Bit9'sacquisitionofCarbonBlackhashelpedfuelinterestinmodernizingendpointdefenses,whichhavebeenrelyingheavilyonsignature-basedtechnologytodetectmalware.
Newconceptsarebeingintroducedthatincorporateendpointagentorsensortechnologytoincreasevisibilityandgiveincidentrespondersmorecontextintoalertsandcontroloverinfectedsystems.
EndpointSTAPisrapidlyevolving.
Theattentiongiventopure-playvendorshaspromptedestablishedsecurityvendorstoaddsimilarspecializedthreatanalysisandprotectioncapabilities.
Therootofmanyoftheseemergingtechnologiesisinhost-basedintrusionpreventionanddigitalforensicscapabilitiesthatidentifythreatsinunderlyingsystemmemory,abnormalapplicationfunctioncalls,andothersignsofunusualsystembehavior.
IDCisawareofAccessData,FireEyeMIR,GuidanceSoftwareEncase,RSAECAT,andotherforensicstoolsthathelprespondersgainvisibilitywhileinvestigatingthescopeofaninfection.
IDC2015IDC#2596679analystsexaminetheseproductscloselytodeterminewhetherthereisreal-timemonitoringandalertingcapabilitiesandthecustomerrequirementsandusecasesthattheproductsfulfill.
METHODOLOGYThisIDCsoftwaremarketsizingandforecastispresentedintermsofpackagedsoftwareandappliancerevenue.
IDCusesthetermpackagedsoftwaretodistinguishcommerciallyavailablesoftwarefromcustomsoftware,nottoimplythatthesoftwaremustbeshrink-wrappedorotherwiseprovidedviaphysicalmedia.
Packagedsoftwareisprogramsorcodesetsofanytypecommerciallyavailablethroughsale,lease,orrental,orasaservice.
Packagedsoftwarerevenuetypicallyincludesfeesforinitialandcontinuedright-to-usepackagedsoftwarelicenses.
Thesefeesmayinclude,aspartofthelicensecontract,accesstoproductsupportand/orotherservicesthatareinseparablefromtheright-to-uselicensefeestructure,orthissupportmaybepricedseparately.
Upgradesmaybeincludedinthecontinuingrightofuseormaybepricedseparately.
AllofthesearecountedbyIDCaspackagedsoftwarerevenue.
Appliancesaredefinedasacombinationofhardware,operatingenvironment,andapplicationsoftwarewheretheyareprovidedasasingleproduct.
Packagedsoftwarerevenueexcludesservicerevenuederivedfromtraining,consulting,andsystemsintegrationthatisseparate(orunbundled)fromtheright-to-uselicensebutdoesincludetheimplicitvalueoftheproductincludedinaservicethatofferssoftwarefunctionalitybyadifferentpricingscheme.
Itisthetotalproductrevenuethatisfurtherallocatedtomarkets,geographicareas,andoperatingenvironments.
Themarketforecastandanalysismethodologyincorporatesinformationfromfivedifferentbutinterrelatedsources,asfollows:Reportedandobservedtrendsandfinancialactivity.
Thisstudyincorporatesreportedandobservedtrendsandfinancialactivityin2014asoftheendofSeptember2015.
IDC'sSoftwareCensusinterviews.
IDCinterviewsallsignificantmarketparticipantstodetermineproductrevenue,revenuedemographics,pricing,andotherrelevantinformation.
Productbriefings,pressreleases,andotherpubliclyavailableinformation.
IDC'ssoftwareanalystsaroundtheworldmeetwithhundredsofsoftwarevendorseachyear.
Thesebriefingsprovideanopportunitytoreviewcurrentandfuturebusinessandproductstrategies,revenue,shipments,customerbases,targetmarkets,andotherkeyproductandcompetitiveinformation.
Vendorfinancialstatementsandrelatedfilings.
Althoughmanysoftwarevendorsareprivatelyheldandchoosetolimitfinancialdisclosures,informationfrompubliclyheldcompaniesprovidesasignificantbenchmarkforassessinginformalmarketestimatesfromprivatecompanies.
IDCalsobuildsdetailedinformationrelatedtoprivatecompaniesthroughin-depthanalystrelationshipsandmaintainsanextensivelibraryoffinancialandcorporateinformationfocusedontheITindustry.
Wefurthermaintaindetailedrevenuebyproductareamodelsonmorethan1,000worldwidevendors.
IDCdemand-sideresearch.
Thisincludesthousandsofinterviewswithbusinessusersofsoftwaresolutionsannuallyandprovidesapowerfulfifthperspectiveforassessingcompetitiveperformanceandmarketdynamics.
IDC'suserstrategydatabasesofferacompellingandconsistenttime-seriesviewofindustrytrendsanddevelopments.
Directconversationswithtechnologybuyersprovideaninvaluablecomplementtothebroadersurvey-basedresults.
2015IDC#25966710Ultimately,thedatapresentedinthisstudyrepresentsIDC'sbestestimatesbasedonthesedatasourcesaswellasreportedandobservedactivitybyvendorsandfurthermodelingofdatathatwebelievetobetruetofillinanyinformationgaps.
ThedatainthisstudyisderivedfromallthesesourcesandenteredintoIDC'sSoftwareMarketForecasterdatabase,whichisthenupdatedonacontinuousbasisasnewinformationregardingsoftwarevendorrevenuebecomesavailable.
Note:Allnumbersinthisdocumentmaynotbeexactduetorounding.
MARKETDEFINITIONThespecializedthreatanalysisandprotectionmarketoverlapstheendpoint,messaging,network,andWebfunctionalmarkets.
Theproductshelpprotectenterprisesfromnewmalwareattacksthatcannotbedetectedbytraditionalsignature-basedtechniques.
TheSTAPproductsuseavarietyofnon-signature-basedprotectionmethodsincluding,butnotlimitedto,sandboxing,behavioralanalysis,fileintegritymonitoring,telemetricheuristics,containerization,netflowanalysis,andthreatintelligence,whichcandetectamalwareattackorcompromisebyidentifyingattackeractivityorsubtlesystemprocesschanges.
Someoftheproductsonlydetectandalert,whileothersmaycontainmalwaretopreventitfromcausingdamage.
Althoughthesefeaturesmayappearinotherproducts,thiscategoryisonlyfordedicatedSTAPsolutions.
TheSTAPmarketismadeupofdistinguishableproductsasopposedtoembeddedfeatureswithinaproduct.
Theabilitytofindandpreventadvancedmalwareultimatelyrequiresdedicatedactivities,andinthisway,itispossibletomeasuretheextentthatenterprisesareconsciouslytakingactionstodealwithadvancedmalware.
TheSTAPmarketisacompetitivemarketthatoverlapsotherlogicalsecurityproductsmarkets(e.
g.
,IAM,network,endpoint,messaging,Web,SVM,and"other"securityproducts).
TheSTAPmarketmustbereportedseparatelyand,furthermore,notaddedtothesevenlogicalsecurityproductsmarkets,otherwisethetotalsecurityproductsmarketfigurewillbeincorrect.
RELATEDRESEARCHIDC'sForecastScenarioAssumptionsfortheICTMarketsandHistoricalMarketValuesandExchangeRates,Version3,2015(IDC#259115,September2015)WorldwideSpecializedThreatAnalysisandProtectionForecast,2015–2019:DefendingAgainsttheUnknown(IDC#256354,May2015)MarketAnalysisPerspective:WorldwideSecurityProducts,2014(IDC#252908,December2014)WorldwideITSecurityProducts2014–2018Forecastand2013VendorShares:ComprehensiveSecurityProductReview(IDC#253371,December2014)IDC'sWorldwideSecurityProductsTaxonomy,2014(IDC#250802,September2014)WorldwideSpecializedThreatAnalysisandProtection2013–2017Forecastand2012VendorShares(IDC#242346,August2013)AboutIDCInternationalDataCorporation(IDC)isthepremierglobalproviderofmarketintelligence,advisoryservices,andeventsfortheinformationtechnology,telecommunicationsandconsumertechnologymarkets.
IDChelpsITprofessionals,businessexecutives,andtheinvestmentcommunitymakefact-baseddecisionsontechnologypurchasesandbusinessstrategy.
Morethan1,100IDCanalystsprovideglobal,regional,andlocalexpertiseontechnologyandindustryopportunitiesandtrendsinover110countriesworldwide.
For50years,IDChasprovidedstrategicinsightstohelpourclientsachievetheirkeybusinessobjectives.
IDCisasubsidiaryofIDG,theworld'sleadingtechnologymedia,research,andeventscompany.
GlobalHeadquarters5SpeenStreetFramingham,MA01701USA508.
872.
8200Twitter:@IDCidc-insights-community.
comwww.
idc.
comCopyrightNoticeThisIDCresearchdocumentwaspublishedaspartofanIDCcontinuousintelligenceservice,providingwrittenresearch,analystinteractions,telebriefings,andconferences.
Visitwww.
idc.
comtolearnmoreaboutIDCsubscriptionandconsultingservices.
ToviewalistofIDCofficesworldwide,visitwww.
idc.
com/offices.
PleasecontacttheIDCHotlineat800.
343.
4952,ext.
7988(or+1.
508.
988.
7988)orsales@idc.
comforinformationonapplyingthepriceofthisdocumenttowardthepurchaseofanIDCserviceorforinformationonadditionalcopiesorWebrights.
[trademark]Copyright2015IDC.
Reproductionisforbiddenunlessauthorized.
Allrightsreserved.
- tierfilemarkets.com相关文档
- promotefilemarkets.com
- Imagefilemarkets.com
- grantedfilemarkets.com
- householdsfilemarkets.com
- indexesfilemarkets.com
- Sourcefilemarkets.com
Megalayer(48元)新增 美国CN2优化线路特价服务器和VPS方案
Megalayer 商家算是新晋的服务商,商家才开始的时候主要是以香港、美国独立服务器。后来有新增菲律宾机房,包括有VPS云服务器、独立服务器、站群服务器等产品。线路上有CN2优化带宽、全向带宽和国际带宽,这里有看到商家的特价方案有增加至9个,之前是四个的。在这篇文章中,我来整理看看。第一、香港服务器系列这里香港服务器会根据带宽的不同区别。我这里将香港机房的都整理到一个系列里。核心内存硬盘IP带宽...

JustHost:俄罗斯/新西伯利亚vps,512MB内存/5GB空间/不限流量/200Mbps/KVM/自由更换IP,$1.57/月
justhost怎么样?justhost是一家俄罗斯主机商,2006年成立,提供各种主机服务,vps基于kvm,有HDD和SSD硬盘两种,特色是200Mbps不限流量(之前是100Mbps,现在升级为200Mbps)。下面是HDD硬盘的KVM VPS,性价比最高,此外还有SSD硬盘的KVM VPS,价格略高。支持Paypal付款。国内建议选择新西伯利亚或者莫斯科DataLine。支持Paypal付...
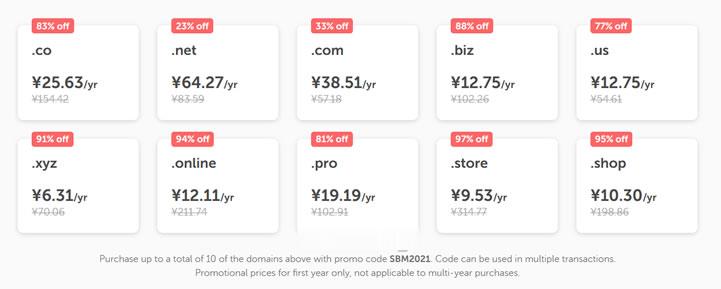
NameCheap优惠活动 新注册域名38元
今天上午有网友在群里聊到是不是有新注册域名的海外域名商家的优惠活动。如果我们并非一定要在国外注册域名的话,最近年中促销期间,国内的服务商优惠力度还是比较大的,以前我们可能较多选择海外域名商家注册域名在于海外商家便宜,如今这几年国内的商家价格也不贵的。比如在前一段时间有分享到几个商家的年中活动:1、DNSPOD域名欢购活动 - 提供域名抢购活动、DNS解析折扣、SSL证书活动2、难得再次关注新网商家...
filemarkets.com为你推荐
-
sherylsandbergLean In是一个怎样的组织老虎数码相机里的传感器CCD和CMO是什么意思?老虎数码我想买个一千左右的数码相机!最好低于一千五!再给我说一下像素是多少?刘祚天你们知道21世纪的DJ分为几种类型吗?(答对者重赏)7788k.com以前有个网站是7788MP3.com后来改成KK130现在又改网站域名了。有知道现在是什么域名么?www.kknnn.com求有颜色的网站!要免费的www.kaspersky.com.cn现在网上又有病毒了?hao.rising.cn如何解除瑞星主页锁定(hao.rising.cn). 不想用瑞星安全助手官人放题SBNS-088 中年男の夢を叶えるセックス やりたい放題! 4(中文字幕)种子下载地址有么?好人一生平安盗车飞侠侠盗飞车飞机怎么弄