setwindows
windows server 2008 企业版 时间:2021-03-01 阅读:()
CopyrightIBMCorporation2006TrademarksKerberizedauthenticationofWindowsTerminalServicePage1of7KerberizedauthenticationofWindowsTerminalServiceUseIBMNetworkAuthenticationServiceasyourKeyDistributionCenteronAIX5.
3SandeepRameshPatilPrashantSodhiyaAugust22,2006DiscoverhowtoconfiguretheMicrosoftWindows2003ServertoauthenticateTerminalServiceuserswiththeIBMNetworkAuthenticationService(IBMNAS)KeyDistributionCenter(KDC)beinghostedontheirAIX5.
3system.
SuchasetupnotonlygivesKerberizedauthenticationforTerminalServiceusers,butitalsoallowsuserstohaveuniformuserIDsandpasswordsacrossAIXandWindowsServersystems.
ItallowsapplicationdeveloperstoexploittheadvantagesofKerberosinteroperabilitybetweenIBMNASandWindowsinKerberizedapplicationsspanningacrosssystems.
IntroductionKerberos,whichprovidesasecuremeansofauthenticationfornetworkusers,isoneofthemostpopularauthenticationmechanisms.
MostmodernoperatingsystemssupportKerberos-based(Version5)authentication.
IBMAIX5.
3alsosupportsKerberos-basedauthentication.
TheIBMversionofKerberosiscalledIBMNetworkAuthenticationService(IBMNAS),anditcanbeinstalledfromAIX5.
3ExpansionPackCDs.
IBMNASforAIXsupportsbothKerberosclientsandKerberosservers.
ManyenterprisesworldwideuseIBMNASforAIXastheKeyDistributionCenter(KDC)fortheirKerberosrealm.
ItisbeingusedinNetworkFileSystem(NFS)Version4deployment,IBMDB2UniversalDatabase(DB2UDB)security,KerberizedAIXintegratedlogin,enterprise-wideauthentication,andmore.
Todaycustomersgenerallyhaveaheterogeneoussetup,withamixofUNIXandWindowssystems.
AmajorchallengeforadministratorswithheterogeneousenvironmentsistohaveuniformuserIDsandpasswordsacrossdifferentsystems,preferablywithacentralizedauthenticationserver.
MicrosoftWindowsServereditionsprovideafacilitycalledTerminalServicesthatarewidelybecomingpopularintheWindowsworld.
ThisfacilityallowsmultipleuserstologintoadeveloperWorksibm.
com/developerWorks/KerberizedauthenticationofWindowsTerminalServicePage2of7Windowsserversimultaneously.
MicrosoftWindowsServereditionsalsosupportKerberos-basedauthentication,whichisinteroperablewithIBMNAS.
Inthisarticle,administratorslearnhowtoconfiguretheMicrosoftWindows2003ServertoauthenticateTerminalServiceuserswiththeIBMNASKDCbeinghostedontheirAIX5.
3system.
SuchasetupnotonlygivesKerberizedauthenticationforTerminalServiceusers,butitalsoallowsuserstohaveuniformuserIDsandpasswordsacrossAIXandWindowsServersystemsandallowsapplicationdeveloperstoexploittheadvantagesofKerberosinteroperabilitybetweenIBMNASandWindowsinKerberizedapplicationsspanningacrosssystems.
Scenario:IBMNASKDConAIXandKerberizedauthenticationofWindowsTerminalServiceWe'lluseascenariothattakesyouthroughthestepsrequiredtosetupIBMNASKDConanAIXsystemandhaveKerberizedauthenticationofWindowsTerminalServicebyconfiguringWindows2003ServertoIBMNASKDC.
Thefollowingdefinitionsareusedintheexampleinthisarticle:KerberosrealmnameAIXKERBEROS.
IN.
IBM.
COMKDC(IBMNAS1.
4)hostname:fsaix11.
in.
ibm.
com,OS:AIX5.
3WindowsTerminalServicehostname:windce14.
in.
ibm.
com,OS:Windows2003Server(ServicePack1withHotfixforArticleID:902336)Kerberosadministratornameadmin/adminFigure1showsthesetupoftheexample.
Figure1.
Examplesetupibm.
com/developerWorks/developerWorksKerberizedauthenticationofWindowsTerminalServicePage3of7InstallingandconfiguringIBMNASServeronAIX5.
3ThissectioncoverstheinstallationandconfigurationofanIBMNASserver(KerberosKDC)onAIX5.
3.
InstallingKerberosKDConAIX5.
3IBMNASisshippedwithAIX5.
3ExpansionPackCDs.
ToinstalltheIBMNASserverpackage,installthekrb5.
server.
rtefileset.
YoucanusethefollowingcommandtoinstalltheNASserverfileset:[root@fsaix11/]#hostnamefsaix11.
in.
ibm.
com[root@fsaix11/]#installp-aqXYgd.
krb5.
serverThenexportthefollowingPATHtoensurethatyouexecuteIBMNAScommandsfromtherespectiveIBMNASdirectories:[root@fsaix11/]#exportPATH=/usr/krb5/sbin:/usr/krb5/bin:$PATHConfiguringKerberosKDConAIX5.
3ToconfigureanIBMNASserveronanAIXmachine,usethecommandinListing1below.
Inthisexample,we'reusingthelegacyconfiguration,wheretheprincipalsarestoredinadatabaseonthelocalfilesystem.
Insteadofthelegacyconfiguration,IBMNASservercanalsobeconfiguredtoLightweightDirectoryAccessProtocol(LDAP)usinganLDAPdirectoryplug-in.
FormoreinformationonconfigurationofIBMNASwithLDAP,seetheIBMNASVersion1.
4AdministrationGuide,shippedwithAIXVersion5.
3ExpansionPackCD.
Listing1.
ConfiguringanIBMNASserveronanAIXmachine[root@fsaix11/]#hostnamefsaix11.
in.
ibm.
com[root@fsaix11/]#/usr/krb5/sbin/config.
krb5-S-din.
ibm.
com-rAIXKERBEROS.
IN.
IBM.
COMInitializingconfiguration.
.
.
Creating/etc/krb5/krb5_cfg_type.
.
.
Creating/etc/krb5/krb5.
conf.
.
.
Creating/var/krb5/krb5kdc/kdc.
conf.
.
.
Creatingdatabasefiles.
.
.
Initializingdatabase'/var/krb5/krb5kdc/principal'forrealm'AIXKERBEROS.
IN.
IBM.
COM'masterkeyname'K/M@AIXKERBEROS.
IN.
IBM.
COM'YouarepromptedforthedatabaseMasterPassword.
ItisimportantthatyouDONOTFORGETthispassword.
EnterdatabaseMasterPassword:Re-enterdatabaseMasterPasswordtoverify:WARNING:nopolicyspecifiedforadmin/admin@AIXKERBEROS.
IN.
IBM.
COM;defaultingtonopolicy.
NotethatpolicymaybeoverriddenbyACLrestrictions.
Enterpasswordforprincipal"admin/admin@AIXKERBEROS.
IN.
IBM.
COM":Re-enterpasswordforprincipal"admin/admin@AIXKERBEROS.
IN.
IBM.
COM":Principal"admin/admin@AIXKERBEROS.
IN.
IBM.
COM"created.
developerWorksibm.
com/developerWorks/KerberizedauthenticationofWindowsTerminalServicePage4of7Creatingkeytable.
.
.
Creating/var/krb5/krb5kdc/kadm5.
acl.
.
.
Startingkrb5kdc.
.
.
krb5kdcwasstartedsuccessfully.
Startingkadmind.
.
.
kadmindwasstartedsuccessfully.
Thecommandcompletedsuccessfully.
BecausetheWindowsKerberosimplementationcurrentlysupportsonlyDES-CBC-MD5andDEC-CBC-CRCencryptiontypes,youneedtochangetheIBMNASKerberosserverdefaultencryptionsettingssothattheWindowsworkstationscanauthenticatetoanIBMNASserver.
YoumustmakethefollowingchangesontheAIXmachine(fsaix11.
in.
ibm.
com,inyourcase)hostingtheIBMNASKDC:Editthe/var/krb5/krb5kdc/kdc.
conffileandchangethevalueofsupported_enctypestohavedes-cbc-md5:normalanddes-cbc-crc:normalatthebeginningoftheencryption-typelist.
Afterediting,thesupported_enctypessectionofthe/var/krb5/krb5kdc/kdc.
conffileshouldlooksimilarto:supported_enctypes=des-cbc-md5:normaldes-cbc-crc:normaldes3-cbc-sha1:normalarcfour-hmac:normalaes256-cts:normalRestarttheAIXNASserverdaemons(forexample,krb5kdcandkadmind)sothattheaboveencryption-typechangestakeeffect.
TorestarttheAIXNASserverdaemons,usethefollowingcommands,asshowninListing2.
Listing2.
RestartingtheAIXNASserverdaemons[root@fsaix11/]#stop.
krb5Stopping/usr/krb5/sbin/krb5kdc.
.
.
/usr/krb5/sbin/krb5kdcwasstoppedsuccessfully.
Stopping/usr/krb5/sbin/kadmind.
.
.
/usr/krb5/sbin/kadmindwasstoppedsuccessfully.
Thecommandcompletedsuccessfully.
[root@fsaix11/]#start.
krb5Startingkrb5kdc.
.
.
krb5kdcwasstartedsuccessfully.
Startingkadmind.
.
.
kadmindwasstartedsuccessfully.
Thecommandcompletedsuccessfully.
RequiredKerberosprincipalsfortheWindowsTerminalServiceusersNowyouneedtocreateKerberosprincipalscorrespondingtotheWindowsTerminalServiceusers(andservices)whowishtohaveKerberizedauthenticationoverthenetwork.
Inthissetup,youwantthe"administrator"userofthewindce14.
in.
ibm.
commachinehostingtheWindowsTerminalServicetobeauthenticatedusingIBMNASKDChostedonfsaix11.
in.
ibm.
com,anAIX5.
3machine.
Youarerequiredtocreateadministratorandhost/windce14.
aixkerberos.
in.
ibm.
comKerberosprincipalsusingthekadmin.
localcommandofIBMNASonfsaix11.
in.
ibm.
com,asshownbelowinListing3.
ibm.
com/developerWorks/developerWorksKerberizedauthenticationofWindowsTerminalServicePage5of7Listing3.
Thekadmin.
localcommand[root@fsaix11/]#kadmin.
localkadmin.
local:ank-pwlaureladministratorWARNING:nopolicyspecifiedforadministrator@AIXKERBEROS.
IN.
IBM.
COM;defaultingtonopolicy.
NotethatpolicymaybeoverriddenbyACLrestrictions.
Principal"administrator@AIXKERBEROS.
IN.
IBM.
COM"created.
kadmin.
local:ank-pwlaurelhost/windce14.
aixkerberos.
in.
ibm.
comWARNING:nopolicyspecifiedforhost/windce14.
aixkerberos.
in.
ibm.
com@AIXKERBEROS.
IN.
IBM.
COM;defaultingtonopolicy.
NotethatpolicymaybeoverriddenbyACLrestrictions.
Principal"host/windce14.
aixkerberos.
in.
ibm.
com@AIXKERBEROS.
IN.
IBM.
COM"created.
TheadministratorisrequiredtocreateKerberosprincipalscorrespondingtoeachWindowsTerminalServiceuserthatneedsKerberosauthentication.
Inthisexample,wearedemonstratingitonlyforthe"administrator"principal.
Windows2003ServerTerminalServicesreadinessIfyouhavealreadydeployedtheWindows2003ServerTerminalServerinyourenvironment,allyouarerequiredtodoisinstallaMicrosoftHotfixforTerminalServices.
ForTerminalServicestoworkwellwithKerberizedauthenticationconfiguredtoIBMNASKDContheWindows2003Server,youmustinstallaHotfixprovidedbyMicrosoftfortheWindowsServer2003-basedTerminalServer.
OnceyouhaveinstalledtheHotfix(ortheproposedworkaround),youareallsettoconfiguretheWindows2003ServertoIBMNASKDCandruntheWindowsTerminalServicewithKerberizedauthentication.
FordetailedinformationoninstallationandconfigurationoftheMicrosoftTerminalServer,seetheappropriateMicrosoftdocumentation.
ConfigureWindows2003Server(Kerberosclient)toIBMNASserverAfterinstallingtheHotfix,youneedtoconfiguretheWindows2003KerberosclienttotheIBMNASserveronAIX5.
3.
Forthat,youneedtodownloadtheResourceKitToolsfromWindows2003ServerCD,whichinstallstheWindowsKerberosutilities(ksetup,ktpass,andsoon).
ToconfiguretheWindows2003ServertoactasaKerberosclienttotheIBMNASserver:1.
MaketheWindowsServer(windce14.
in.
ibm.
com)apartofyourKerberosworkgroupbysettingittoyourKerberosdomainusingtheksetupcommand:C:\>hostnamewindce14C:\>ksetup/setdomainAIXKERBEROS.
IN.
IBM.
COM2.
ConfiguretheWindowsServermachinetotheKerberosrealmbyspecifyingtheKerberosrealmnameandKerberosservername,asshownbelow:C:\>ksetup/addkdcAIXKERBEROS.
IN.
IBM.
COMfsaix11.
in.
ibm.
com3.
Setthelocalmachineaccountpassword,asfollows:C:\>ksetup/setmachpasswordlaureldeveloperWorksibm.
com/developerWorks/KerberizedauthenticationofWindowsTerminalServicePage6of7ThispasswordmustmatchthepasswordusedwhenyoucreatedtheKerberoshostprincipal(host/windce14.
aixkerberos.
in.
ibm.
com)byinvokingankfromkadmin.
local,explainedearlier.
4.
MaptheKerberosusertoalocalWindowsuser.
Thecommandbelowmapsthelocalwindowsadministratorusertoadministrator@AIXKERBEROS.
IN.
IBM,aKerberosprincipal:C:\>ksetup/mapuseradministrator@AIXKERBEROS.
IN.
IBM.
COMadministrator5.
Restartthecomputerforthechangestotakeeffect.
Figure2summarizesallthestepsexecutedaboveontheWindowsmachine.
Figure2.
ConfigurationofWindows2003ServerasKerberosclienttoAIXKDCTestingthesetupYouarenowallsettoexercisetheKerberizedauthenticationofWindowsTerminalServiceusersagainstIBMNASKDChostedontheAIXV5.
3machine.
LogintotheWindowsServermachine(windce14.
in.
ibm.
com)usingtheRemoteDesktopConnectionfromanyofyourWindowsdesktopmachines.
Onconnection,itpresentsyouwiththelogonscreenforthewindce14.
in.
ibm.
commachine.
SelectLogonto.
YoushouldseethattheKerberosrealmyoucreatedisalsopresentinthedrop-downlist.
NowenteryourKerberosusernameandthepassword(inthiscase,theusernameisadministratorandthepasswordislaurel),selectAIXKERBEROS.
IN.
IBM.
COM(KerberosRealm)ibm.
com/developerWorks/developerWorksKerberizedauthenticationofWindowsTerminalServicePage7of7inthe"Logonto"option,andselectOK.
ThiswillthencarryouttheKerberizedauthenticationprocess,anduponsuccesswilllogtheTerminalServiceuserintotheWindowsmachine.
Figure3showstheRemotelogintotheWindowsservermachine.
Figure3.
KerberizedauthenticationofWindowsTerminalServiceusersagainstIBMNASKDCConclusionThisarticleexplainshowadministratorscanusetheIBMNASKDConAIX5.
3forauthenticationofWindows2003TerminalService.
Thisshouldhelpsimplifyadministration,anditalsoallowsuserstohavecommonuserIDsandpasswordsacrossAIXandWindowsTerminalServicesystems.
CopyrightIBMCorporation2006(www.
ibm.
com/legal/copytrade.
shtml)Trademarks(www.
ibm.
com/developerworks/ibm/trademarks/)
3SandeepRameshPatilPrashantSodhiyaAugust22,2006DiscoverhowtoconfiguretheMicrosoftWindows2003ServertoauthenticateTerminalServiceuserswiththeIBMNetworkAuthenticationService(IBMNAS)KeyDistributionCenter(KDC)beinghostedontheirAIX5.
3system.
SuchasetupnotonlygivesKerberizedauthenticationforTerminalServiceusers,butitalsoallowsuserstohaveuniformuserIDsandpasswordsacrossAIXandWindowsServersystems.
ItallowsapplicationdeveloperstoexploittheadvantagesofKerberosinteroperabilitybetweenIBMNASandWindowsinKerberizedapplicationsspanningacrosssystems.
IntroductionKerberos,whichprovidesasecuremeansofauthenticationfornetworkusers,isoneofthemostpopularauthenticationmechanisms.
MostmodernoperatingsystemssupportKerberos-based(Version5)authentication.
IBMAIX5.
3alsosupportsKerberos-basedauthentication.
TheIBMversionofKerberosiscalledIBMNetworkAuthenticationService(IBMNAS),anditcanbeinstalledfromAIX5.
3ExpansionPackCDs.
IBMNASforAIXsupportsbothKerberosclientsandKerberosservers.
ManyenterprisesworldwideuseIBMNASforAIXastheKeyDistributionCenter(KDC)fortheirKerberosrealm.
ItisbeingusedinNetworkFileSystem(NFS)Version4deployment,IBMDB2UniversalDatabase(DB2UDB)security,KerberizedAIXintegratedlogin,enterprise-wideauthentication,andmore.
Todaycustomersgenerallyhaveaheterogeneoussetup,withamixofUNIXandWindowssystems.
AmajorchallengeforadministratorswithheterogeneousenvironmentsistohaveuniformuserIDsandpasswordsacrossdifferentsystems,preferablywithacentralizedauthenticationserver.
MicrosoftWindowsServereditionsprovideafacilitycalledTerminalServicesthatarewidelybecomingpopularintheWindowsworld.
ThisfacilityallowsmultipleuserstologintoadeveloperWorksibm.
com/developerWorks/KerberizedauthenticationofWindowsTerminalServicePage2of7Windowsserversimultaneously.
MicrosoftWindowsServereditionsalsosupportKerberos-basedauthentication,whichisinteroperablewithIBMNAS.
Inthisarticle,administratorslearnhowtoconfiguretheMicrosoftWindows2003ServertoauthenticateTerminalServiceuserswiththeIBMNASKDCbeinghostedontheirAIX5.
3system.
SuchasetupnotonlygivesKerberizedauthenticationforTerminalServiceusers,butitalsoallowsuserstohaveuniformuserIDsandpasswordsacrossAIXandWindowsServersystemsandallowsapplicationdeveloperstoexploittheadvantagesofKerberosinteroperabilitybetweenIBMNASandWindowsinKerberizedapplicationsspanningacrosssystems.
Scenario:IBMNASKDConAIXandKerberizedauthenticationofWindowsTerminalServiceWe'lluseascenariothattakesyouthroughthestepsrequiredtosetupIBMNASKDConanAIXsystemandhaveKerberizedauthenticationofWindowsTerminalServicebyconfiguringWindows2003ServertoIBMNASKDC.
Thefollowingdefinitionsareusedintheexampleinthisarticle:KerberosrealmnameAIXKERBEROS.
IN.
IBM.
COMKDC(IBMNAS1.
4)hostname:fsaix11.
in.
ibm.
com,OS:AIX5.
3WindowsTerminalServicehostname:windce14.
in.
ibm.
com,OS:Windows2003Server(ServicePack1withHotfixforArticleID:902336)Kerberosadministratornameadmin/adminFigure1showsthesetupoftheexample.
Figure1.
Examplesetupibm.
com/developerWorks/developerWorksKerberizedauthenticationofWindowsTerminalServicePage3of7InstallingandconfiguringIBMNASServeronAIX5.
3ThissectioncoverstheinstallationandconfigurationofanIBMNASserver(KerberosKDC)onAIX5.
3.
InstallingKerberosKDConAIX5.
3IBMNASisshippedwithAIX5.
3ExpansionPackCDs.
ToinstalltheIBMNASserverpackage,installthekrb5.
server.
rtefileset.
YoucanusethefollowingcommandtoinstalltheNASserverfileset:[root@fsaix11/]#hostnamefsaix11.
in.
ibm.
com[root@fsaix11/]#installp-aqXYgd.
krb5.
serverThenexportthefollowingPATHtoensurethatyouexecuteIBMNAScommandsfromtherespectiveIBMNASdirectories:[root@fsaix11/]#exportPATH=/usr/krb5/sbin:/usr/krb5/bin:$PATHConfiguringKerberosKDConAIX5.
3ToconfigureanIBMNASserveronanAIXmachine,usethecommandinListing1below.
Inthisexample,we'reusingthelegacyconfiguration,wheretheprincipalsarestoredinadatabaseonthelocalfilesystem.
Insteadofthelegacyconfiguration,IBMNASservercanalsobeconfiguredtoLightweightDirectoryAccessProtocol(LDAP)usinganLDAPdirectoryplug-in.
FormoreinformationonconfigurationofIBMNASwithLDAP,seetheIBMNASVersion1.
4AdministrationGuide,shippedwithAIXVersion5.
3ExpansionPackCD.
Listing1.
ConfiguringanIBMNASserveronanAIXmachine[root@fsaix11/]#hostnamefsaix11.
in.
ibm.
com[root@fsaix11/]#/usr/krb5/sbin/config.
krb5-S-din.
ibm.
com-rAIXKERBEROS.
IN.
IBM.
COMInitializingconfiguration.
.
.
Creating/etc/krb5/krb5_cfg_type.
.
.
Creating/etc/krb5/krb5.
conf.
.
.
Creating/var/krb5/krb5kdc/kdc.
conf.
.
.
Creatingdatabasefiles.
.
.
Initializingdatabase'/var/krb5/krb5kdc/principal'forrealm'AIXKERBEROS.
IN.
IBM.
COM'masterkeyname'K/M@AIXKERBEROS.
IN.
IBM.
COM'YouarepromptedforthedatabaseMasterPassword.
ItisimportantthatyouDONOTFORGETthispassword.
EnterdatabaseMasterPassword:Re-enterdatabaseMasterPasswordtoverify:WARNING:nopolicyspecifiedforadmin/admin@AIXKERBEROS.
IN.
IBM.
COM;defaultingtonopolicy.
NotethatpolicymaybeoverriddenbyACLrestrictions.
Enterpasswordforprincipal"admin/admin@AIXKERBEROS.
IN.
IBM.
COM":Re-enterpasswordforprincipal"admin/admin@AIXKERBEROS.
IN.
IBM.
COM":Principal"admin/admin@AIXKERBEROS.
IN.
IBM.
COM"created.
developerWorksibm.
com/developerWorks/KerberizedauthenticationofWindowsTerminalServicePage4of7Creatingkeytable.
.
.
Creating/var/krb5/krb5kdc/kadm5.
acl.
.
.
Startingkrb5kdc.
.
.
krb5kdcwasstartedsuccessfully.
Startingkadmind.
.
.
kadmindwasstartedsuccessfully.
Thecommandcompletedsuccessfully.
BecausetheWindowsKerberosimplementationcurrentlysupportsonlyDES-CBC-MD5andDEC-CBC-CRCencryptiontypes,youneedtochangetheIBMNASKerberosserverdefaultencryptionsettingssothattheWindowsworkstationscanauthenticatetoanIBMNASserver.
YoumustmakethefollowingchangesontheAIXmachine(fsaix11.
in.
ibm.
com,inyourcase)hostingtheIBMNASKDC:Editthe/var/krb5/krb5kdc/kdc.
conffileandchangethevalueofsupported_enctypestohavedes-cbc-md5:normalanddes-cbc-crc:normalatthebeginningoftheencryption-typelist.
Afterediting,thesupported_enctypessectionofthe/var/krb5/krb5kdc/kdc.
conffileshouldlooksimilarto:supported_enctypes=des-cbc-md5:normaldes-cbc-crc:normaldes3-cbc-sha1:normalarcfour-hmac:normalaes256-cts:normalRestarttheAIXNASserverdaemons(forexample,krb5kdcandkadmind)sothattheaboveencryption-typechangestakeeffect.
TorestarttheAIXNASserverdaemons,usethefollowingcommands,asshowninListing2.
Listing2.
RestartingtheAIXNASserverdaemons[root@fsaix11/]#stop.
krb5Stopping/usr/krb5/sbin/krb5kdc.
.
.
/usr/krb5/sbin/krb5kdcwasstoppedsuccessfully.
Stopping/usr/krb5/sbin/kadmind.
.
.
/usr/krb5/sbin/kadmindwasstoppedsuccessfully.
Thecommandcompletedsuccessfully.
[root@fsaix11/]#start.
krb5Startingkrb5kdc.
.
.
krb5kdcwasstartedsuccessfully.
Startingkadmind.
.
.
kadmindwasstartedsuccessfully.
Thecommandcompletedsuccessfully.
RequiredKerberosprincipalsfortheWindowsTerminalServiceusersNowyouneedtocreateKerberosprincipalscorrespondingtotheWindowsTerminalServiceusers(andservices)whowishtohaveKerberizedauthenticationoverthenetwork.
Inthissetup,youwantthe"administrator"userofthewindce14.
in.
ibm.
commachinehostingtheWindowsTerminalServicetobeauthenticatedusingIBMNASKDChostedonfsaix11.
in.
ibm.
com,anAIX5.
3machine.
Youarerequiredtocreateadministratorandhost/windce14.
aixkerberos.
in.
ibm.
comKerberosprincipalsusingthekadmin.
localcommandofIBMNASonfsaix11.
in.
ibm.
com,asshownbelowinListing3.
ibm.
com/developerWorks/developerWorksKerberizedauthenticationofWindowsTerminalServicePage5of7Listing3.
Thekadmin.
localcommand[root@fsaix11/]#kadmin.
localkadmin.
local:ank-pwlaureladministratorWARNING:nopolicyspecifiedforadministrator@AIXKERBEROS.
IN.
IBM.
COM;defaultingtonopolicy.
NotethatpolicymaybeoverriddenbyACLrestrictions.
Principal"administrator@AIXKERBEROS.
IN.
IBM.
COM"created.
kadmin.
local:ank-pwlaurelhost/windce14.
aixkerberos.
in.
ibm.
comWARNING:nopolicyspecifiedforhost/windce14.
aixkerberos.
in.
ibm.
com@AIXKERBEROS.
IN.
IBM.
COM;defaultingtonopolicy.
NotethatpolicymaybeoverriddenbyACLrestrictions.
Principal"host/windce14.
aixkerberos.
in.
ibm.
com@AIXKERBEROS.
IN.
IBM.
COM"created.
TheadministratorisrequiredtocreateKerberosprincipalscorrespondingtoeachWindowsTerminalServiceuserthatneedsKerberosauthentication.
Inthisexample,wearedemonstratingitonlyforthe"administrator"principal.
Windows2003ServerTerminalServicesreadinessIfyouhavealreadydeployedtheWindows2003ServerTerminalServerinyourenvironment,allyouarerequiredtodoisinstallaMicrosoftHotfixforTerminalServices.
ForTerminalServicestoworkwellwithKerberizedauthenticationconfiguredtoIBMNASKDContheWindows2003Server,youmustinstallaHotfixprovidedbyMicrosoftfortheWindowsServer2003-basedTerminalServer.
OnceyouhaveinstalledtheHotfix(ortheproposedworkaround),youareallsettoconfiguretheWindows2003ServertoIBMNASKDCandruntheWindowsTerminalServicewithKerberizedauthentication.
FordetailedinformationoninstallationandconfigurationoftheMicrosoftTerminalServer,seetheappropriateMicrosoftdocumentation.
ConfigureWindows2003Server(Kerberosclient)toIBMNASserverAfterinstallingtheHotfix,youneedtoconfiguretheWindows2003KerberosclienttotheIBMNASserveronAIX5.
3.
Forthat,youneedtodownloadtheResourceKitToolsfromWindows2003ServerCD,whichinstallstheWindowsKerberosutilities(ksetup,ktpass,andsoon).
ToconfiguretheWindows2003ServertoactasaKerberosclienttotheIBMNASserver:1.
MaketheWindowsServer(windce14.
in.
ibm.
com)apartofyourKerberosworkgroupbysettingittoyourKerberosdomainusingtheksetupcommand:C:\>hostnamewindce14C:\>ksetup/setdomainAIXKERBEROS.
IN.
IBM.
COM2.
ConfiguretheWindowsServermachinetotheKerberosrealmbyspecifyingtheKerberosrealmnameandKerberosservername,asshownbelow:C:\>ksetup/addkdcAIXKERBEROS.
IN.
IBM.
COMfsaix11.
in.
ibm.
com3.
Setthelocalmachineaccountpassword,asfollows:C:\>ksetup/setmachpasswordlaureldeveloperWorksibm.
com/developerWorks/KerberizedauthenticationofWindowsTerminalServicePage6of7ThispasswordmustmatchthepasswordusedwhenyoucreatedtheKerberoshostprincipal(host/windce14.
aixkerberos.
in.
ibm.
com)byinvokingankfromkadmin.
local,explainedearlier.
4.
MaptheKerberosusertoalocalWindowsuser.
Thecommandbelowmapsthelocalwindowsadministratorusertoadministrator@AIXKERBEROS.
IN.
IBM,aKerberosprincipal:C:\>ksetup/mapuseradministrator@AIXKERBEROS.
IN.
IBM.
COMadministrator5.
Restartthecomputerforthechangestotakeeffect.
Figure2summarizesallthestepsexecutedaboveontheWindowsmachine.
Figure2.
ConfigurationofWindows2003ServerasKerberosclienttoAIXKDCTestingthesetupYouarenowallsettoexercisetheKerberizedauthenticationofWindowsTerminalServiceusersagainstIBMNASKDChostedontheAIXV5.
3machine.
LogintotheWindowsServermachine(windce14.
in.
ibm.
com)usingtheRemoteDesktopConnectionfromanyofyourWindowsdesktopmachines.
Onconnection,itpresentsyouwiththelogonscreenforthewindce14.
in.
ibm.
commachine.
SelectLogonto.
YoushouldseethattheKerberosrealmyoucreatedisalsopresentinthedrop-downlist.
NowenteryourKerberosusernameandthepassword(inthiscase,theusernameisadministratorandthepasswordislaurel),selectAIXKERBEROS.
IN.
IBM.
COM(KerberosRealm)ibm.
com/developerWorks/developerWorksKerberizedauthenticationofWindowsTerminalServicePage7of7inthe"Logonto"option,andselectOK.
ThiswillthencarryouttheKerberizedauthenticationprocess,anduponsuccesswilllogtheTerminalServiceuserintotheWindowsmachine.
Figure3showstheRemotelogintotheWindowsservermachine.
Figure3.
KerberizedauthenticationofWindowsTerminalServiceusersagainstIBMNASKDCConclusionThisarticleexplainshowadministratorscanusetheIBMNASKDConAIX5.
3forauthenticationofWindows2003TerminalService.
Thisshouldhelpsimplifyadministration,anditalsoallowsuserstohavecommonuserIDsandpasswordsacrossAIXandWindowsTerminalServicesystems.
CopyrightIBMCorporation2006(www.
ibm.
com/legal/copytrade.
shtml)Trademarks(www.
ibm.
com/developerworks/ibm/trademarks/)
- setwindows相关文档
- 服务器windows server 2008考试复习选择题
- 安装windows-server-2003实验操作报告
- 用户Windows server 2003FTP服务器不同用户的管理
- 服务器08679-windows-server-2003网络管理项目实训教程习题参考答案
- 服务器windows server 2008网络操作系统期末复习题全
- 群集windows-server-2012-hyper-v群集图文教程word版
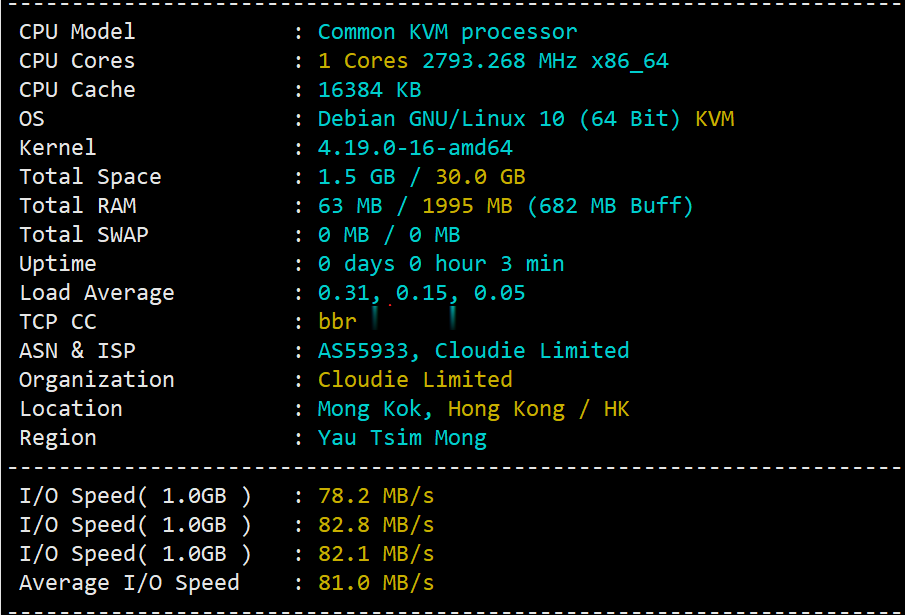
hostyun评测香港原生IPVPS
hostyun新上了香港cloudie机房的香港原生IP的VPS,写的是默认接入200Mbps带宽(共享),基于KVM虚拟,纯SSD RAID10,三网直连,混合超售的CN2网络,商家对VPS的I/O有大致100MB/S的限制。由于是原生香港IP,所以这个VPS还是有一定的看头的,这里给大家弄个测评,数据仅供参考!9折优惠码:hostyun,循环优惠内存CPUSSD流量带宽价格购买1G1核10G3...
盘点618年中大促中这款云服务器/VPS主机相对值得选择
昨天有在"盘点2021年主流云服务器商家618年中大促活动"文章中整理到当前年中大促618活动期间的一些国内国外的云服务商的促销活动,相对来说每年年中和年末的活动力度还是蛮大的,唯独就是活动太过于密集,而且商家比较多,导致我们很多新人不懂如何选择,当然对于我们这些老油条还是会选择的,估计没有比我们更聪明的进行薅爆款新人活动。有网友提到,是否可以整理一篇当前的这些活动商家中的促销产品。哪些商家哪款产...

百纵科技(19元/月),美国洛杉矶10G防御服务器/洛杉矶C3机房 带金盾高防
百纵科技官网:https://www.baizon.cn/百纵科技:美国云服务器活动重磅来袭,洛杉矶C3机房 带金盾高防,会员后台可自助管理防火墙,添加黑白名单 CC策略开启低中高.CPU全系列E52680v3 DDR4内存 三星固态盘列阵。另有高防清洗!美国洛杉矶 CN2 云服务器CPU内存带宽数据盘防御价格1H1G10M10G10G19元/月 购买地址2H1G10M10G10G29元/月 购买...

windows server 2008 企业版为你推荐
-
百度k站被百度k站之后你一般是怎么处理的如何免费开通黄钻如何免费开通黄钻??缓冲区溢出教程适合黑客初级学者使用的黑客工具有那些 、天天酷跑刷积分教程天天酷跑积分怎么刷最快?伪静态怎么做伪静态?arm开发板新手入门应如何选择 ARM 开发板?网站联盟网站联盟的运作流程今日热点怎么删除怎么删除手机百度实时热点如何建立一个网站如何建立一个网站iphone越狱后怎么恢复苹果越狱后怎么恢复出厂设置